Looking Beyond the Hype
- By Sean Lawlor
- Mar 01, 2019
The past few years have seen significant advancements
in computing power. With this, machines seem to have
a greater ability to learn about us and participate in
our lives. Whether through product purchase suggestions
on Amazon.com and other retail outlets or in our
business and professional pursuits, machines are busy learning everywhere
around us. Recently, the market has become flooded with buzz
words relating to this type of work.
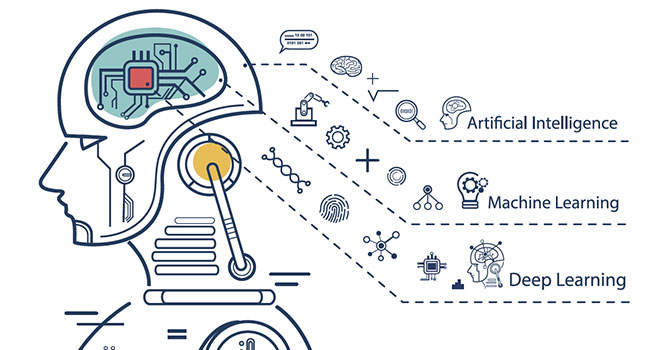
Learning the Proper Terms
Artificial Intelligence, Machine Learning, and Deep Learning are
often used inaccurately and interchangeably. Given the significant
advancements that have been made in this field, especially in the
physical security industry, it is important that we be clear about these
terms and their application. Using the term AI loosely only serves to
misrepresent what machine learning can do and has the potential to
generate misguided and unrealistic expectations.
Artificial Intelligence. AI is a broad term that first appeared in
published research in 1956. For years, we understood AI as it appeared
in pop culture, which lead to questions of a robot’s emotional
capacity or their ability to take over the world. AI denotes a fully
functional artificial brain that can reason, evolve, self-learn, and make
human-like decisions. Currently, we are many years (or decades) away
from this. Using the term artificial intelligence (or AI) related to technology
or applications today can be inaccurate and potentially raise
unrealistic expectations for those considering the technology.
Today’s examples of what many consider to be AI in our lives—
Deep Blue beating a top chess player, Siri recognizing a song, Amazon
suggesting a new book—are really examples of increasingly
small computers running a series of algorithms, searching through
huge databases, or doing a lot of calculations very quickly. With their
faster computing power and processing speeds, our current machines
are able to comb through a huge amount of data to provide deeper
insights. These results can be more accurately categorized as guesses
that can help us make decisions more quickly and efficiently.
Machine Learning. ML is an area of artificial intelligence that
uses data to help a computer improve performance without being explicitly
programmed. Static programming provides a computer with
a set of instructions that do not change over time. Machine learning
allows programmers to enable a computer to assess and alter its computational
processes through training. Specifically, a computer is programmed
with algorithms that enable it to determine which features
of an input it should use in the identification process to efficiently
produce the most accurate output. In a simple example, a computer
might be trained to determine whether color or shape is a better indicator
for correctly classifying a new input.
Working primarily with data in the form of language, text, video,
or images, machine learning uses statistical techniques to enable computer
systems to solve problems, make decisions and predictions, or
improve the efficiency of specific, narrowly defined tasks.
Supervised and Unsupervised
Machine Learning
The two most prevalent types of machine learning are Unsupervised
and Supervised: Unsupervised machine learning, also called Data
Mining, tackles very narrow problems by analyzing unstructured
data—data that has not been organized or labeled in advance—in
order to find patterns. With unsupervised machine learning, the computer
is looking for discernable patterns in the data and searching for
an unknown output or “ground truth.” One of the main focuses in
unsupervised machine learning is anomaly detection. In this case, the
computer identifies points in a dataset or stream that are outside the
normal range without this range being pre-defined.
In supervised machine learning, computers are “trained” to properly
classify inputs. This training occurs by providing the computer
with structured datasets—data that has been organized or labeled in
a predefined manner—that correlate thousands of possible inputs
with corresponding labels that the computer understands.
The computer learns these correlations, through training, in order
to be able to apply its understanding to new inputs. Once the
computer has ingested and classified a new input, programmers must
evaluate the “truthfulness” or accuracy of the output that the computer
generates.
The programmer must tell the computer how accurate its classification
is in order to train the computer to improve its ability to
recognize new inputs. For example, if you label and input millions
of images of roses and petunias into the computer with their associated
labels, through supervised machine learning, the computer will
ideally be able to differentiate between future images of roses and
petunias at a tolerable rate.
Deep Learning and Working with
Structured and Unstructured Data
One of the sub-disciplines under AI includes research in neural
networks. Working with structured data, this research analyzes the
relationship between inputs and outputs to gain new insights. Deep
learning, also known as deep neural networks, is a specific formulation
of neural networks that also works with structured data. What is
exciting about deep learning is that the accuracies gained lately have
often even exceeded what humans can do with specific tasks.
What’s Achievable Today
with Deep Learning
In the physical security industry, we are achieving increased accuracy
using deep learning to solve structured problems—problems that involve
knowing what the output of the data should generally be. For
example, automatic license plate recognition (ALPR) is a structured
problem because, when we train our algorithms, we work with a data
set of raw ALPR images, including letters, numbers, and symbols, to
arrive at a classified output. In this case, the output is an image of
license plate XYZ123.
At Genetec, we are actively using deep learning for purpose-built
solutions that rely on identifying trends and dependencies between
features present in the data itself. We are currently using deep learning
in AutoVu, our ALPR system, to increase the accuracy and veracity
rates of license plate tag reads. By applying computer vision
algorithms, we have greatly reduced false positive reads for law enforcement
officers when they identify and stop a vehicle of interest.
Similarly, KiwiVision Privacy Protector has also been working with
deep learning to improve the accuracy of its anonymization tool.
Genetec Citigraf is another example of one of the products that
leverages advanced machine learning algorithms to estimate how
different types of crime influence the risk of other crimes occurring
in the future. For example, it can determine how close in time and
space a robbery has to occur to your home to increase the risk of
your home being robbed. In this case, there is no “ground truth”
in the original problem and the answers are learned from the data.
To allow us to pre-emptively handle failures before they occur, we
are also using unsupervised machine learning to help our systems
predict when they will become unstable. Currently, Security Center
provides warnings when you have used 90 percent of the available
disk space. Our goal is to have the system inform you that you will
exceed available disk space in x number of days when you are only
at 10 percent usage.
Limitations
While advances in deep learning can help us realize greater operational
efficiency, it is important to acknowledge that deep learning is
not the ‘be-all and end-all’ associated with AI. In fact, it cannot yet
teach itself new tasks nor automatically make sense of data through
unsupervised learning.
It also has certain limitations. For instance, it can be difficult for users
to interpret deep learning methods when trying to identify the steps
that a machine takes to take a decision. In addition, it is still limited since
it requires a lot of data for training in order to capture complex trends.
However, we are seeing significant benefits with our current applications.
Data Stewardship
When it comes to machine learning, at Genetec our aim is to provide
end-users with highly analyzed data that will guide them towards
making accurate, critical decisions for verified results. The exploratory
phases of creating a data science-based solution begins with data.
In order to be granted access to data, we need to demonstrate to our
customers and partners that we are proper stewards of data and can
be trusted with it. An important step towards building that trust is
being clear about what data science can and cannot do, which starts
with debunking popular assumptions.
We are still a long way away from true AI—machines cannot give
meaning to, or make sense of something, on their own. Applications
can be developed to use pre-programmed algorithms to discover patterns
in data or trained to correctly recognize and classify different
inputs. Working with these algorithms we can also allow them to
make their own improvements to perform their
tasks more efficiently. This is a starting point towards
unlocking the potential of machine learning
that will allow us to find even more innovative
approaches to protecting our everyday and developing
safer, more secure environments.
This article originally appeared in the March 2019 issue of Security Today.