Kwikset Kevo’s Latest Upgrade Introduces Free Unlimited Guest eKeys
Kwikset introduces its latest Kevo upgrade, giving users the ability to send free and unlimited guest electronic keys (eKeys) 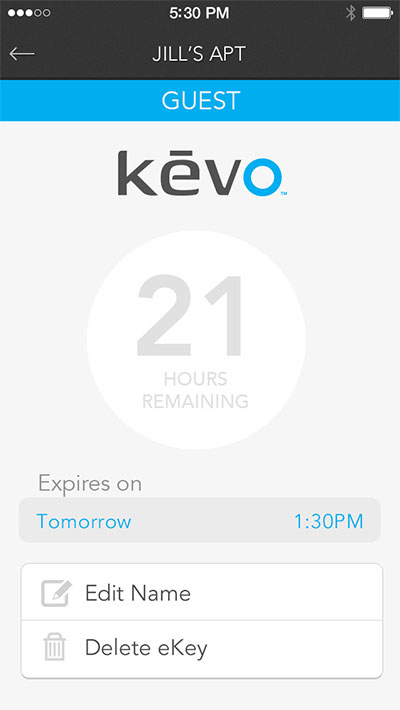 to recipients, and with a scheduled eKey, set day and time constraints for regular house guests like babysitters, dog-walkers and contractors. Kevo owners can update their Kevo mobile app and lock firmware to enable these new types of eKeys.
to recipients, and with a scheduled eKey, set day and time constraints for regular house guests like babysitters, dog-walkers and contractors. Kevo owners can update their Kevo mobile app and lock firmware to enable these new types of eKeys.
"We're always looking for ways to improve the Kevo experience, and we hope this upgrade shows our customers that we're listening," said Keith Brandon, director, residential access solutions. "Since Kevo's been on the market, our customers have asked for free eKeys that let them give access anytime to friends or neighbors without paying for a new key. Now our unlimited Guest eKeys let them do that. We're also introducing Scheduled eKeys to give homeowners the convenience of setting date and time constraints."
Mobile App Upgrade
With new free and unlimited Guest eKeys, users can give recipients unrestricted access for a 24-hour period. Owners also have the option to delete Guest eKeys manually before the 24-hour access expires. From giving a neighbor day-long access to keep an eye on your kids, or letting in a weekend guest who beats you home from a busy day at work, the Guest eKey provides ultimate convenience and flexibility.
The new Scheduled eKey enhances home access control by allowing users to set day and time constraints right from their phones. Ideal for house cleaners, dog walkers, nannies or others that need regular access at pre-determined times, like on Tuesdays and Thursdays from 1-3 p.m. Kevo owners can schedule these eKeys to be active prior to sending, so they don't have to remember to grant or revoke access to these users in real time.
"The Kevo technology platform was built with the future in mind by having the ability to add new features and enhancements to the firmware in the lock, in addition to the mobile app,” said Phil Dumas, UniKey founder and president. “This capability allows the lock to get smarter over time."
Additional Kevo App Features
Managing eKeys using the Kevo mobile app is easy, letting owners control their home security at any time with their smartphones. Additional Kevo app features include:
- History log that monitors lock activity and tracks eKey users;
- Optional push notifications when an eKey locks or unlocks the door;
- Ability to share eKeys in just a few clicks;
- Ability to temporarily disable or completely delete unwanted users from Kevo;
- Touch-to-open convenience with authorized Kevo deadbolts; and
- Kevo web portal that offers the same management features via a web browser.
Since its introduction as the first-to-market, Bluetooth-enabled smart lock in October 2013, Kevo has turned the smartphone into a key and revolutionized the way users share and manage access to their homes. The Bluetooth-enabled deadbolt offers the only touch-to-open technology that lets users unlock the door with a simple touch while their authorized smartphone remains in their purse or pocket.
Kevo comes with two eKeys that can be reassigned as Scheduled or Anytime eKeys as well as free, unlimited Guest eKeys. To grant long-term access to additional guests, Kevo owners can purchase additional Anytime or Scheduled eKeys in the app for $1.99.