
Some common areas and issues to keep growing your business, not your security risk.
- By Gary Brown
- Apr 26, 2019

Beyond user privacy, we’ve seen GDPR impact companies in other ways.

EmCare Inc., a physician-staffing company, says a data breach has exposed personal information for about 31,000 patients
- By Jessica Davis
- Apr 23, 2019
All of your personal data can be easily accessible and vulnerable to hackers.
- By Susan Alexandra
- Apr 22, 2019

Hospitals are often in the news due to data breaches, and email hacks are often the cause.
- By Kayla Matthews
- Apr 19, 2019

Many companies are employing System and Organization Controls reports before procuring vendors' services.
- By Brad Thies
- Apr 18, 2019

What went wrong?
- By Kayla Matthews
- Apr 18, 2019

Six things you can do to be proactive against potential cyber crimes.
- By Kayla Matthews
- Apr 17, 2019

Are voice-enabled devices making you more vulnerable to cyberattack?
- By Sydny Shepard
- Apr 16, 2019

While no system is foolproof, biometrics are vastly more accurate and secure ways to identify patients because they measure a physical trait (something you are) rather than a piece of knowledge (something you know e.g., passwords, ssn, PIN).
- By Michael Fox
- Apr 16, 2019

No one really knows why airlines have become a target as of late but with the rate of attacks this high, something is definitely going on.
- By Matthew Walker-Jones
- Apr 08, 2019

Facebook is in trouble again.

Strong passwords, two-factor authentication and good cyber hygiene will keep your personal information protected while browsing popular social media accounts.
- By Susan Alexandra
- Apr 04, 2019

Toyota's servers in Japan have been hacked, leaving millions of pieces of data left vulnerable.
- By Sydny Shepard
- Apr 02, 2019
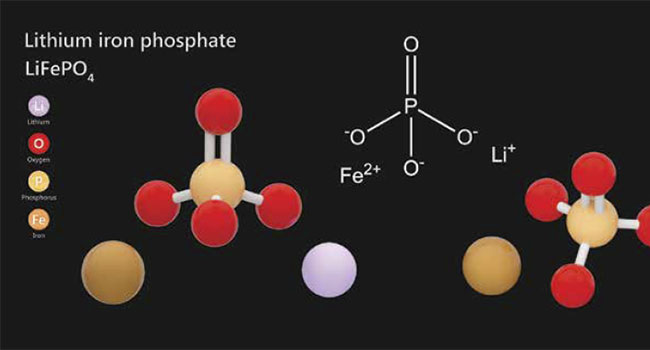
One of the primary criteria for any surveillance, access or security system is the requirement for a consistent and reliable power source, as even the most complex and expensive system solutions will be rendered useless if power is interrupted.
- By JR Andrews
- Apr 01, 2019

As cybercrime continues to plague companies of all sizes, across all industries both public and private, we wanted to take this opportunity to explore options that can help protect your data and your business.
- By Rich Aycock
- Apr 01, 2019

The breach exposed diagnostic results, healthcare numbers and personal contact information.
- By Sydny Shepard
- Mar 29, 2019

New proposal creates stricter safeguards against data breaches, protects more private consumer information and enhances data security and reporting requirements.
- By Sydny Shepard
- Mar 26, 2019

Everyone should be changing their Facebook passwords after it was discovered all use passwords have been left unencrypted and searchable in plaintext.

2FA is more secure than single-factor methods only requiring a password, but it's not an impenetrable method.
- By Kayla Matthews
- Mar 25, 2019