
According to Aite Group, a research and advisory firm, losses incurred by account takeovers at contact centers are expected to reach $775 million in 2020, nearly double the amount from just five years ago.
- By Dr. Kornel Laskowski
- Jun 01, 2019

A new technology that can covertly detect weapons is being considered by Utah officials to secure large events and public spaces.
- By Sydny Shepard
- May 24, 2019

Amazon Alexa users that enable Alexa Guard on their smart speakers can now take advantage of a few security features.
- By Sydny Shepard
- May 16, 2019

The use of facial recognition by police might cease to exist in San Francisco if adopts a ban on the technology.
- By Sydny Shepard
- May 14, 2019
Ever, a photo storage and backup app, reportedly trained a commercial facial recognition system using millions of images uploaded to the service without notifying users.
- By Jessica Davis
- May 10, 2019

Due to the growing use of biometrics to counter security threats, the biometric technology market is expected to bloom over the next few years.
- By Sydny Shepard
- Apr 22, 2019

Lyft has announced two new features to enhance the security and safety of the riders using the Lyft platform.
- By Sydny Shepard
- Apr 18, 2019

Convenience stores and mini marts have traditionally installed surveillance cameras to deter crime and encourage safety, but too often these have provided images that lacked detail, particularly in low light conditions.
- By Del Williams
- Apr 01, 2019
Like many metropolitan cities, Hartford, CT has its share of crimes. And solving those crimes usually involves sifting through an overwhelming amount of data.
- By Kevin Taylor
- Apr 01, 2019
The confusion I hear in the industry starts with the definitions of these terms: artificial intelligence (AI), machine learning (deep and shallow), and analytics. Some believe these things are all the same and use them interchangeably.

Video surveillance management is becoming increasingly sophisticated in terms of operational capabilities, including the type and scope of analytics available.
- By Peter Ainsworth
- Apr 01, 2019
The Internet of Things Cybersecurity Improvement Act aims to establish a bare minimum of security standards for IoT devices used by the federal government
- By Jessica Davis
- Mar 13, 2019
Artificial intelligence continues to redefine the capabilities of physical security systems and shape customer demands.
- By Fredrik Wallberg
- Mar 01, 2019

The following predictions for ISC West 2019 dive deeper into how these innovations, among others, will help move the security industry forward.
- By Joe Oliveri
- Mar 01, 2019

As key stakeholders look to implement AI into their workflow, many find that security and safety is a commonsense place to begin.
- By Brent Boekestein
- Mar 01, 2019
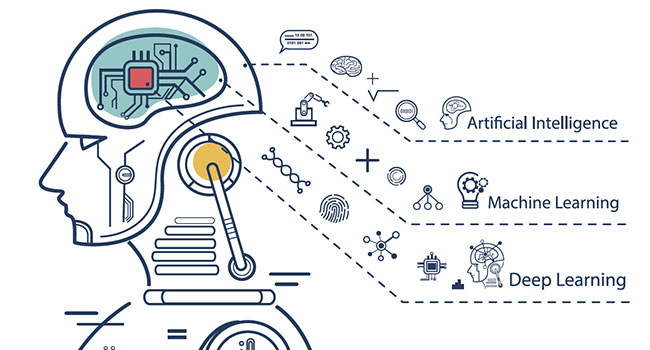
The past few years have seen significant advancements in computing power. With this, machines seem to have a greater ability to learn about us and participate in our lives.
- By Sean Lawlor
- Mar 01, 2019

When dealing with airport and border security, we need databases, we need to share information and we need law enforcement.
- By Martin Zizi
- Mar 01, 2019

Samsung’s new “in-display” Ultrasonic Fingerprint system certified by FIDO Alliance as meeting globally recognized standards for biometric recognition performance and Presentation Attack Detection (PAD)

A new security system uses artificial intelligence to detect guns with up to 99 percent accuracy.
- By Sydny Shepard
- Feb 13, 2019

The Defense Intelligence Agency has released a new report detailing the security challenges the United States face in outer space.
- By Sydny Shepard
- Feb 13, 2019