
A Clear Understanding of Security in the Cloud
- By Gretchen Marx
- Sep 19, 2013
 One of the most significant benefits of cloud computing is the ability to respond to rapidly changing workloads. While this provides real value, it can also present security challenges. In fact, numerous studies cite security as the number one inhibitor to cloud adoption.
One of the most significant benefits of cloud computing is the ability to respond to rapidly changing workloads. While this provides real value, it can also present security challenges. In fact, numerous studies cite security as the number one inhibitor to cloud adoption.
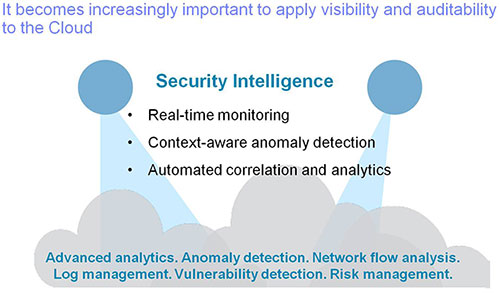
In a traditional data center environment, the IT infrastructure is protected by a demilitarized zone, a DMZ made up of firewalls and intrusion detection and prevention systems. When applications and data are shifted to the cloud, the concept of a single perimeter no longer holds up. How is the security team to see and understand what it going on in the cloud when it’s, well…cloudy? Organizations can adopt an improved cloud security and risk posture with advanced analytics and security intelligence capabilities.
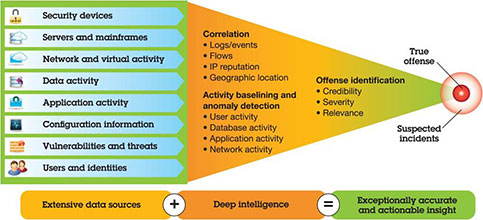
Build in the ability to see through the cloud. Security devices, such as those validating user IDs and passwords, or monitoring network traffic, capture enormous amounts of data needed for regulatory compliance and forensic investigation. The challenge is to find meaningful signals about a potential attack or security risk in the sea of data points. An advanced Security Information and Event Management (SIEM) system extends the traditional SIEM methodology with real-time analytics and correlation – Security Intelligence – providing visibility into both the data center and the cloud infrastructure.
To really understand what is happening in private, hybrid, and public clouds, security teams need to look into communications at a much deeper level. They need to see beyond simply who is participating in an exchange and discover when the content of these interactions include recognizable data patterns, such as social security numbers, credit card numbers, text—including terms like “ID” or “password”—or other protected information.
Because virtualized server traffic cannot be collected using traditional monitoring technologies, organizations need solutions to monitor virtual environments in support of cloud computing. Virtual flow collectors provide application-layer visibility into all virtual network traffic for advanced security intelligence in the cloud.
Application-aware, flow data is obtained from a deep examination and inspection of every packet, which also allows for advanced threat detection through analysis of packet payload content. Correlating this flow information with network and security events, vulnerabilities, identity information and threat intelligence is the optimal way to obtain a complete and accurate view of an organization’s cloud security posture.
 Virtual flow collectors can also analyze port-mirrored traffic for a physical network switch, which helps bridge the gap between physical and virtual devices in the cloud. Collectors that run on a virtual server and do not require additional hardware are a highly cost-effective solution.
Virtual flow collectors can also analyze port-mirrored traffic for a physical network switch, which helps bridge the gap between physical and virtual devices in the cloud. Collectors that run on a virtual server and do not require additional hardware are a highly cost-effective solution.
Next-generation SIEMs provide advanced incident analysis via correlation of flow data with log data, providing accurate prioritization of incident data and reduction of false positives by correlating security events and network traffic within and between both cloud and traditional environments.
An advanced SIEM should include a dashboard that:
With advanced security intelligence accessible in real-time, through the single pane of an integrated dashboard, it is possible to see in the cloud.
About the Author
Gretchen Marx is a manager for cloud security strategy at IBM.