 In light of the recent Target and Nordstrom security breaches – as well as dozens of others that have occurred in the past couple of years – companies have been scrambling to find the best security technology. Companies are exploring options from standalone iris-scanning devices and biometric tokens to implementing more complicated passwords as a barrier to entry. In a world where security measures are always changing, but to date, have failed to keep our identities safe, what is the best way to keep our personal material truly secure?
In light of the recent Target and Nordstrom security breaches – as well as dozens of others that have occurred in the past couple of years – companies have been scrambling to find the best security technology. Companies are exploring options from standalone iris-scanning devices and biometric tokens to implementing more complicated passwords as a barrier to entry. In a world where security measures are always changing, but to date, have failed to keep our identities safe, what is the best way to keep our personal material truly secure?
For many people, convenience is the most important aspect of any new technology. How can it make our lives a little bit easier? Can it help us to save a precious few minutes in our busy days? When companies develop new technology to maintain our privacy and security, though, convenience is often the first feature to be disregarded.
Luckily, we have reached a point in our technological advancements where security and convenience can coexist, and the reality is that it doesn’t involve another password, key fob, access card or username. The solution is what I like to call “token-less.”
To date, many companies have been relying heavily on the use of tokens as a means of identity assertion – need I remind you of what happened to RSA? These tokens are not only burdensome to the user – another thing to purchase, carry and try not to lose – but they are often also expensive at a corporate level. The omnipresence of these tokens is of concern, because they are repeatedly lost, stolen or hacked. It’s time that we learn our lesson.
Biometrics – The Pros and Cons
Today, there are two types of biometric identity assertion systems that exist for consumers: biometric tokens and integrated biometric platforms. Both methods acquire biometric information from the user, but the means of acquisition and level of security are where these two technologies differ.
Of the two, biometric tokens are the most problematic option for more reasons than the requirement of buying a new gadget and carrying an extra piece of hardware. Tokens can also be easily lost or stolen, creating an unnecessary inconvenience for the user. Once the biometric token is obtained by a hacker, it can be easily spoofed, and the user’s information is no longer secure. This, in turn, diminishes both the convenience and security for the user as a result.
So, what can we do to eradicate tokens? Studies from Ericsson and PayPal have shown that biometrics on smartphones are the preferred means of identity assertion. The main reason for this is the fact that we already carry with us all of the necessary hardware, making it the most convenient solution. The successful adoption of a product and continued support by consumers is always going to be centered on convenience. Users want their identities to be secure, but surprisingly, not at the cost of their convenience.
The Solution
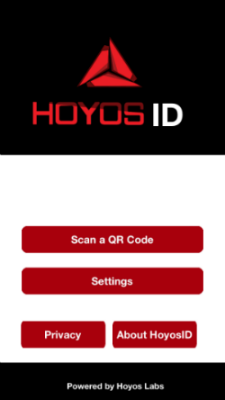 At this year’s CES, Hoyos Labs introduced a solution to address this issue. This solution will enable consumers and corporate users to assert their identities securely, accurately and conveniently without additional hardware. Hoyos Labs’ HoyosID is a free app that utilizes smartphones as biometrics acquisition devices through using an app that runs on iPhones and Androids. Instead of using usernames and passwords, users can log-in with biometrics – including periocular, iris and facial – and their smartphones and nothing else.
At this year’s CES, Hoyos Labs introduced a solution to address this issue. This solution will enable consumers and corporate users to assert their identities securely, accurately and conveniently without additional hardware. Hoyos Labs’ HoyosID is a free app that utilizes smartphones as biometrics acquisition devices through using an app that runs on iPhones and Androids. Instead of using usernames and passwords, users can log-in with biometrics – including periocular, iris and facial – and their smartphones and nothing else.
When a user clicks on a webpage’s log-in, the HoyosID app is automatically opened on the smartphone. After acquiring iris biometrics, the app logs-in the user in under 30 seconds. If someone other than the authorized user tries to access the phone’s information, the HoyosID intrusion detection system blocks the attempt.
Unlike most hacks that we hear about on the news, which result in millions of consumers being breached at once, the HoyosID architecture forces hackers to first appropriate the smartphone and then attempt to hack one user at a time. For this reason, it is essential to have an end-to-end biometric solution that possesses a secure back-end, which is where biometric solutions that are hardware alone tend to fail.
By using iris and periocular biometrics, people can perform a variety of tasks on their smartphones including the ability to make financial transactions quickly, seamlessly and securely. These daily tasks that require us to log-in with a username and password often take up more time than we may realize, especially when we forget our log-in information. The eradication of these small inconveniences will add up to a lot more for the consumer, especially when the ease-of-use enhances security.
For those who wish for a day when biometric solutions are both secure and convenient that time has finally come. Identity assertion and authentication now successfully combine biometrics and smartphones, moving technological progress forward toward a future without passwords or tokens.