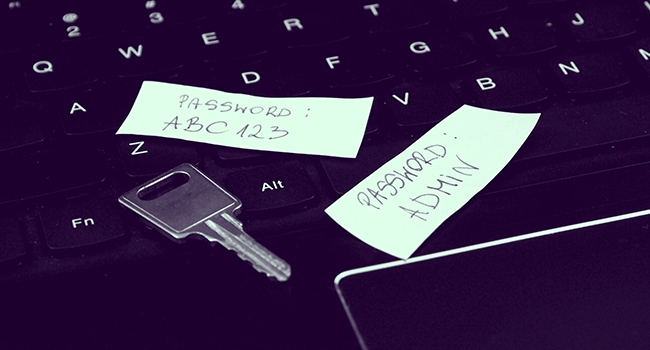
Employee Cybersecurity Habits Worsen
According to the survey, three of every four respondents admitted that they reuse passwords across accounts, an increase from the 56 percent of respondents who admitted the same in the survey’s 2014 edition.
- By Jessica Davis
- Nov 26, 2018
Despite growing concerns about cybersecurity and the number of data breach incidents in the news, many employees still have bad cybersecurity habits, according to a SailPoint survey.
For its 2018 Market Pulse Survey, identity governance provider SailPoint surveyed employees at organizations with at least 1,000 employees in the United States, the United Kingdom, Australia, France, Germany, Italy and Spain.
According to the survey, three of every four respondents admitted that they reuse passwords across accounts, an increase from the 56 percent of respondents who admitted the same in the survey’s 2014 edition. The survey also found that 87 percent of people between the ages of 18-25 reuse passwords, including almost one-half who do so across work and personal accounts.
Almost a third (31 percent) of respondents said they had deployed software without getting the authorization of their organization’s IT department, an increase from 20 percent in 2014. This practice, called “shadow IT,” doesn’t take security into consideration and was, in part, attributed to efforts to boost efficiency at work.
More than half (55 percent) of respondents said their organization’s IT department can cause inconvenience. Thirteen percent of employees said that if they thought they’d been hacked, they wouldn’t immediately alert their IT team, and 49 percent of employees even said they’d blame the IT department for a cyberattack if it happened via an employee being hacked.
About the Author
Jessica Davis is the Associate Content Editor for 1105 Media.