
FBI Facial Recognition Database Contains Images of the Innocent
- By Ginger Hill
- Apr 15, 2014
Documents obtained by the Electronic Frontier Foundation discovered that the massive facial recognition database, Next Generation Identification (NGI), 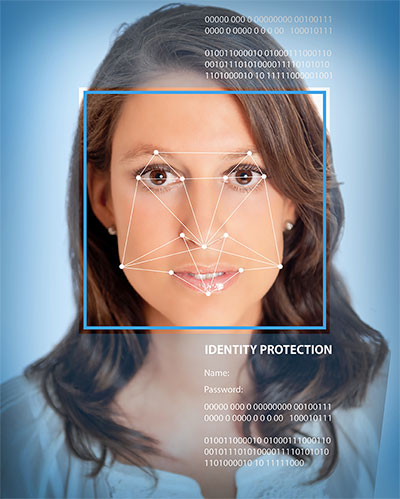 currently being built by the FBI will have 52 million photos by 2015. That’s 36 million more photos than the database had in the middle of 2013! Besides that, 4.3 million images included in this database were obtained for “non-criminal purposes.” Guess Big Brother is always watching…even the innocent.
currently being built by the FBI will have 52 million photos by 2015. That’s 36 million more photos than the database had in the middle of 2013! Besides that, 4.3 million images included in this database were obtained for “non-criminal purposes.” Guess Big Brother is always watching…even the innocent.
It’s not exactly clear where the photos came from, but it is speculated that jobs requiring a background check, fingerprints or an identification photo sent them to the FBI.
NGI will have both criminal and non-criminal records side-by-side, which is different from the FBI’s fingerprint database that kept them separate. Any searches ran will query the entire database so that even those who haven’t been arrested for a crime could have their facial images pop up. (I sure hope the FBI agent doesn’t misread an image, seeing a non-criminal as a criminal! Case of mistaken identity?!)
Facial recognition seems to be a dual-edged sword when it comes to privacy issues. This technology can improve lives, but it can also be seen as an invasion of privacy. In the case of the FBI’s NGI database, I feel that if a person is innocent, then they shouldn’t have anything to worry about, but I can say that I have a problem with my facial image being displayed side-by-side with criminals. Maybe the FBI needs to consider keeping criminal images and non-criminal images separate.
About the Author
Ginger Hill is Group Social Media Manager.