Electric Guard Dog has been a supporter of Supply Chain and Information Sharing and Analysis Center (ISAC) since 2008 and currently is one of the sponsors of the website. In the last six months, our social media program has received attention for reposting ISAC’s Be On the Lookout (BOLO’s) posts in an effort to raise awareness of where and how often cargo theft is happening (Twitter: @stoptheft and @jackdemao). After the publication of the SC ISAC 2013 annual report, it’s time to review some critical numbers.
What is the SC-ISAC?
The SC-ISAC was created as a result of Presidential Directive in 1998. Because 90% of the nation’s critical infrastructures are owned and operated by the private sector, it was decided a public and private partnership was needed to share information about threats, vulnerabilities and incidents to help protect the critical infrastructures of the United States.
SC-ISAC has been gathering and sharing cargo theft reports for six years. SC-ISAC and CargoNet jointly announced they will merge their information sharing analysis later this year to improve reporting and information sharing.
Critical Numbers of the 2013 Report
The single biggest standout in the SC-ISAC 2013 Cargo Theft report is that for the first time since 2005, there’s a decrease in the total number of reported cargo thefts: 811, down from 947 recorded in 2012. While this is great news, it’s important to note that reporting is uneven. FreightWatch’s annual cargo theft report cited a tie between 2012 & 2013: Both had the highest number of reported cargo thefts in the history of reporting. Additionally, it’s important to note that cargo theft is an underreported and misreported crime
As prevention is the goal, awareness of where, when and why may help:
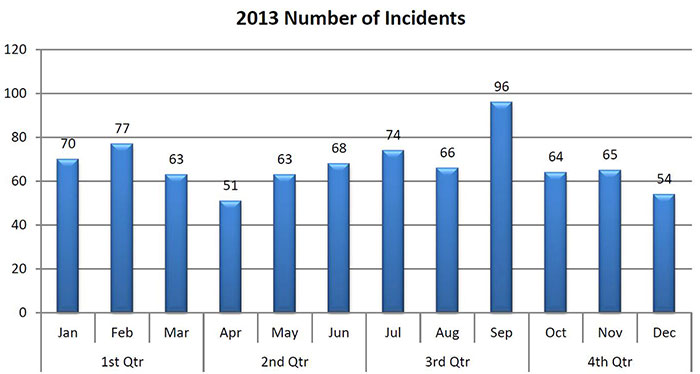
- Which Month? Cargo theft spikes drastically in September, due in part to retailers initiating preparation for Black Friday.
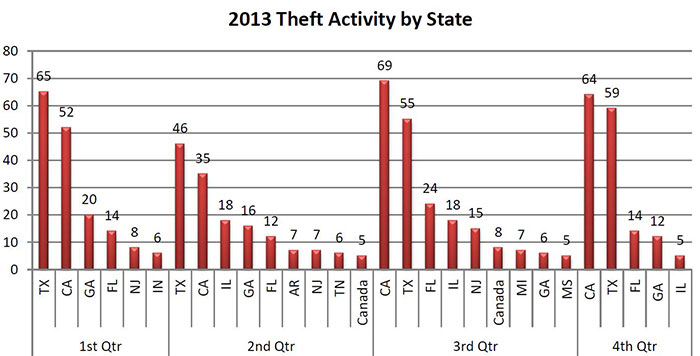
- Which States? California, Texas, Florida and Georgia top the list. But 31 out of the lower 48 states report cargo theft.
- Where Do Cargo Thieves Strike? While fictitious pickups are all over the news, the overwhelming primary targets are still carrier facilities, drop lots and truck stops.
- When Do They Strike? Weekends continue to be the primary focus, topped only by three day weekends in terms of risk level.
- Which Tractors? Almost half of all the equipment stolen is tractors. Freightliner is the runaway favorite to steal in terms of model, quite possibly driven by market share. Kenworth, Peterbilt and International follow in descending order.
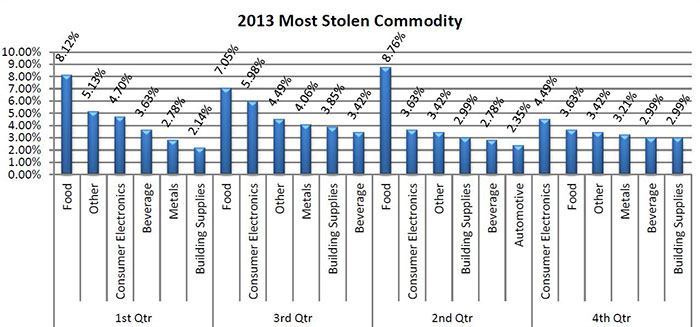
- What Is Stolen? Food is once again the favorite bounty, driven by the ease of fencing it. Consumer electronics made a stronger showing than previous years, while metals and beverages increased in popularity. Clothing and accessories declined.
- Cost Per Load? In addition to the possibility of reduced cargo theft, another positive trend in 2013 was that loss rates have reduced by an average of $95,000, from almost twice that level in 2012. Again the data is representative but probably not precise.
For a more thorough primer on understanding and preventing cargo theft, security authority J.J. Coughlin’s book Cargo Crime is an outstanding resource. Coughlin does an excellent job of explaining how cargo theft affects the industry as well as explores a variety of security options available to commercial companies including a summary of his experience with the Electric Guard Dog which he refers to as “Tried and true…Each and every time I went from having numerous breaches a week to absolutely nothing.”
Additionally, there’s still time to register for the 2nd Annual Mid-America Cargo & Equipment Theft Seminar in Springfield Missouri June 24th and 25th. The event is free but requires registration by June 10th.
SC-ISAC represents an outstanding partnership between law enforcement, truckers, shippers and security vendors. As a team, this group helps supply chain industries defend themselves against ongoing attacks estimated to amount to $35 billion in losses annually. Electric Guard Dog is proud to be a sponsor of the SC_ISAC database and active in regional cargo theft councils.