Online Exclusive: DDoS Attacks Fuel the Need for Modern Protection Methods
DDoS attack prevention is nearly impossible: it’s difficult to track down hackers, whereas it’s easy and inexpensive to launch a DDoS attack.
- By Dave Larson
- Jun 24, 2016
Nearly every day there is a headline brandishing the news of yet another distributed denial of service (DDoS) attack on some major organization. Many other organizations experience DDoS attacks on a daily basis, but those attacks don’t make headline news. It’s an alarming situation, globally. In a recent survey of IT security professionals and network operators at the RSA Conference 2016, 31% of respondents stated that their enterprise experiences DDoS attacks weekly or daily.
This survey also asked participants about their current methods of handling the DDoS threat; nearly one third (30%) of respondents still rely on traditional security infrastructure products (firewall, IPS, load balancers) to protect their businesses from DDoS attacks.
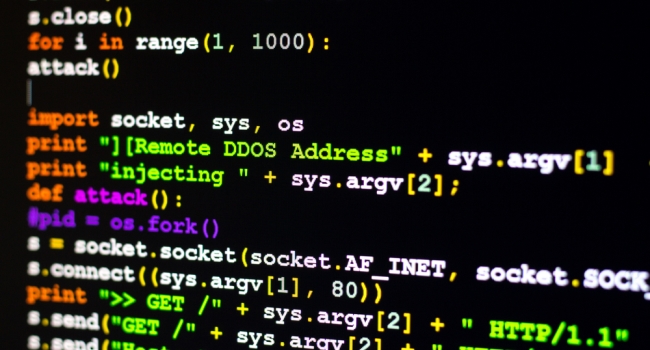
DDoS attack prevention is nearly impossible: it’s difficult to track down hackers, whereas it’s easy and inexpensive to launch a DDoS attack. DDoS attacks are likely to increase rather than go away. However, technology is available today to effectively detect and block attacks to prevent network outages and disruptions. The appliance sits at the network edge, monitoring and mitigating DDoS attack traffic in real time. The solution does not pull attack traffic deeper into the network to a scrubbing center environment, does not rely on human intervention, and does not rely on legacy tools or techniques that some network and security departments use. Rather, it blocks a wide range of DDoS attacks, while maintaining full connectivity and avoiding the disruption of legitimate traffic.
More Than an Availability Issue
Although hackers often launch DDoS attacks purely to create a nuisance by taking a website offline, it’s becoming very common for hackers to launch “Dark DDoS” attacks that distract IT security staff while the hackers launch malware or infiltrate sensitive databases. In all of these cases, the DDoS attacks are low-threshold, short-duration attacks that escape the attention of IT security staff; such attacks may not cripple a website but they can negatively affect network or application performance.
These attacks are far more sophisticated, deceptive and frequent. They are no longer designed simply to deny service, but to deny security, by acting as a camouflage to mask more sinister activities – usually data theft and network infiltration.
How to Deal with DDoS Attacks
Businesses need to understand that the danger is real and this class of attack is happening in their environment more often than they think. Internet media outlets, corporations, government agencies, service providers and the like cannot wait until an attack happens before taking steps for protection.
An organization’s security posture is only as good as their ability visualize the security events in the environment. A robust modern DDoS solution will provide both instantaneous visibility into DDoS events as well as long-term trend analysis to identify adaptations in the DDoS landscape and deliver corresponding proactive detection and mitigation techniques. Automatic DDoS mitigation is available today to eradicate the threat to your business and eliminate both the service availability and security impact.
The Corero SmartWall Threat Defense System (TDS) is designed to detect and respond to a large spectrum of DDoS attacks; ranging from high volume denial of service attempts to blended multi-vector threats, as well as low and slow application layer attacks. Further, the solution detects, analyzes and responds to DDoS attacks by inspecting raw Internet traffic at line rate and identifying the threat within the first few packets of any given attack.
About the Author
Dave Larson, Chief Operating Officer is responsible for directing the Corero technology strategy as the company continues to invest in its next phase of growth: providing next generation DDoS attack and cyber threat defense solutions for the Service Provider and Hosting Provider segments. Larson brings over 20 years of experience in the network security, data communication, and data center infrastructure industries. Most recently, Larson served as Chief Technology Officer for HP Networking and Vice President of the HP Networking Advanced Technology Group. In this role he was responsible for creating the long-term technology vision and strategy for HP Networking across a variety of product divisions and geographies.