Layered Approach
IoT is used to create smart homes, buildings and numerous other end points
- By Jeff Whitney
- May 01, 2017
The security department has long held responsibility for
the physical protection of assets, infrastructure and
people. The operation and protection of electronic
data systems has been the responsibility of the IT department.
Today, we increasingly see the blurring of
these lines with the movement of surveillance, access control, life
safety and other physical security systems onto IP-based network
technology.
The IT approach to layered security for systems, infrastructure
and data is increasingly impacting the security department, and with
good reason. Recent cyberattacks have revealed vulnerabilities beyond
traditional IT systems and infrastructure, uncovering the potential
threat of attack on and through a wider range of network
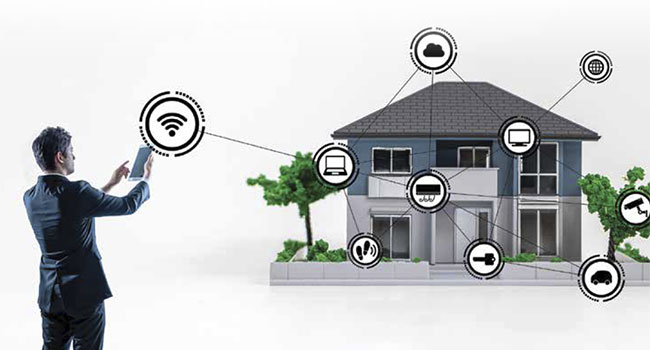
connected devices. The Internet of Things (IoT) is rapidly growing
as network connectivity blurs the line between computing devices,
appliances, vehicles and industrial equipment. IoT is used to create
smart homes and buildings, network enabled appliances, aircraft,
automobiles, ships and trains. It is found across every market segment.
While consumers and industry professionals are excited about
the benefits, cybersecurity experts increasingly warn about the vulnerabilities
that IoT introduces to traditionally secure infrastructure.
Many manufacturers of surveillance cameras, access control and
other security systems have considered their products to be edge devices,
relying on the IT department to provide network protection in
limiting access only to those authorized to do so. This view is changing
as more manufacturers and their customers understand that any
device connected to the network requires basic cybersecurity protection
in the current threat environment.
Akamai, a vendor of content delivery network services, detailed
in its Q3 2015 State of the Internet Security Report a 180 percent yearover-
year increase from 2014 to 2015 in Distributed Denial of Service
(DDoS) attacks. Other sources agree that attacks are dramatically
increasing. Verisign, a Virginia-based infrastructure and security company,
reported in the Verisign Distributed Denial of Service Trends
Report for the 2nd quarter of 2016 that that the frequency of DDoS
cyberattacks increased by 75 percent from the same period a year before.
Industry analyst Gartner estimated in a 2014 press release that
by 2020 more than 25 percent of identified attacks on enterprises will
involve IoT network devices.
Security systems are not immune. The September 2016 attack on
Krebsecurity.com and France-based Internet hosting firm OHV was
executed using over 140,000 network cameras and DVRs. The devices
were transformed into robotic attackers or “bots” by an infection of
the Mirai malware.
The Washington Post reported that 70 percent of the video cameras
across the U.S. capital were infected with ransomware. 123 of
187 NVRs had their data encrypted by the infection in the days prior
to the Trump Presidential Inauguration in January 2017. Other network-
enabled cameras and DVRs have been reported in the media
to secretly connect to sites in China. Data, video and images have reportedly been uploaded to these remote locations without the consent
or awareness of the user. Other cameras have been infected with
malware within seconds of being connected to the Internet, or as being
easily hacked.
While there is reason for action and a need for more education,
there is no cause for panic as the security industry is responding. The
challenge faced by manufacturers of network-enabled security products—
including surveillance cameras—is to balance ease of installation
and ongoing operation with the protection of the device, the
network and the connected infrastructure.
A product with extremely strong cybersecurity protection may
turn away customers by being too restrictive or complex for their
needs. Conversely, a product that is exceptionally easy to setup and
use may be a gateway to cyberattack.
Finding the balance between these two factors while meeting the
requirements of IT is a challenge to be solved by manufacturers.
Arecont Vision relies on its in-house developed Massively Parallel
Image Processing architecture and FPGA (field programmable gate
array) technology to eliminate or mitigate cybersecurity risks and enable
camera updates. The company also takes that further by developing
its own feature and not licensing third-party code for core
features. This eliminates the risk of hidden backdoors or of malicious
code lurking unsuspected and undetected. Other manufacturers will
have their own approaches to cybersecurity.
Being prepared is the best cybersecurity defense, regardless of the
products used. The following dozen recommendations are starting
points for any security organization formulating their own cybersecurity
polices.
Choose products that provide security protection while balancing
the user experience. Only devices that include basic security protection
such user IDs and 16 digit ASCII passwords should be allowed
on the network. The administration interface must balance ease of
installation with adequate cybersecurity protection, without making
the device unduly complicated to use and manage.
Segregate the network. Good design policy is to separate and
firewall cameras, access control, alarm, sensors, and IT systems onto
individual networks or sub-nets. Sharing a single network between
different applications increases the risk of both performance issues,
and both exposure to and the success of a cyberattack. Eliminating
unnecessary connections to the wider corporate network and to the
global Internet can also reduce the risk of successful cyberattacks.
Update firmware. All cameras, servers, NVRs/DVRs, storage devices,
switches, routers, WiFi access points and any other networkconnected
devices should be regularly updated with the latest available
manufacturer firmware to eliminate security holes. No device
that cannot be fully updated with new security measures, features or
enhancements should ever be connected to the network, and a policy
should be enforced to ensuring such updates are performed.
Limit authorization and access to only those who need it. Limit
physical and network access to individual systems, data and infrastructure
to only those who require that access. Enforce password
changes on an appropriate cycle and with any departure of employees
and contractors formerly with access.
Change default password settings. An increasing number of cyberattacks
are made using default IDs and passwords. Cameras, DVRs
and other security systems now join computers, storage and security
systems as potential network access points for a cyberattack, and often
have less security included.
No device should be allowed to connect to the network until the
default user ID and password have been reset after commissioning.
Organizations should have a strong password policy that defines
password rules and frequently requires password changes. Use a secure
password management system to keep track.
Virus scan any device or media before attaching it to the network.
All computers and media used to install or update network cameras,
servers, NVRs or storage devices should be virus scanned with up-todate
protection/detection software for malignant code before being
connected to or loaded into a shared network.
Apply special protection to cameras covering sensitive areas and
limit access. Laws limit where video recording can occur, what can be
recorded, what use can be made of it, and even who can view it. The
security system designer needs to be an expert on these local requirements
and adhere to them.
A good policy is to never install a camera anywhere you would
not want others to see the scene being covered. Sensitive areas or
personal space may not be the best choice for a camera location, particularly
with the risk of a cyberattack.
Educate your team. Employees need to be aware and educated
of the risks and challenges of cybersecurity prevention, detection,
mitigation and recovery in advance of an incident. Accidental or unintentional
exposure is major risk factor in exposing a business or
organization to cyberattack, and education is the best defense.
Integrate and follow IT and security department guidelines for devices
and access. Integrate with established IT and security department
guidelines. Follow industry guidelines, policies and regulations
as best practices to address everything from remote access, cloud networks,
unsecured networks, Bring Your Own Device (BYOD) policies,
network monitoring and data safekeeping.
Conduct regular cybersecurity reviews and assessments. Both the
IT and security departments should conduct regular cybersecurity
reviews and assessments of their infrastructure, systems and policies
throughout the year.
Preplan for cyberattack responses. Many organizations have risk assessment
and response strategies, designed for a wide range of potential
disasters and catastrophic events. Cybersecurity needs to be included
to deal with mitigation and recovery in the event of any incident.
Build and keep a disaster recovery up to date. Have a disaster recovery
plan in place before a catastrophic failure or data breach occurs.
Be sure to keep the plan up to date. Consider making commercial
cybersecurity insurance part of the program.
Establishing these types of security policy recommendations, tailored
to fit the needs of the organization, will prevent many cybersecurity
risks and help to mitigate the impact of those that are not.
Employee education is also of critical importance. Organizations
such as the Security Industry Association, ASIS International, the
Cybersecurity Policy and Research Institute, the Electronic Privacy
Information Center, and many colleges and universities are among
many that offer actionable information on cybersecurity. They are
excellent places to start learning more about how
to protect an organization.
By taking these actions, organizations can be
well on their way to cybersecurity awareness and
protection.
This article originally appeared in the May 2017 issue of Security Today.