Brandjacking isn't new, but you should be aware of the ways you could be getting scammed.
You recently got an email from a company you're familiar with, such as Netflix, and the email tells you that something is wrong with your payment. You'll need to re-enter your credit card information for your entertainment to continue streaming. The email looks authentic enough, so you click.
Upon further inspection, however, you realize this is not the Netflix you know and love but rather a scammer phishing for your credit card information. What is this new trend and how can we prevent it?
Cybersecurity experts are calling this phishing scam "brandjacking." The term is defined as an activity whereby someone acquires or otherwise assumes the online identity of another entity for the purposes of acquiring that person's or business' brand equity.
In layman's terms, that means someone is pretending to be someone their not, like catfishing for businesses but riskier.
Brandjacking isn't exactly "new" but it is getting a lot of attention the past few years given the rise of social media and the ability to create a quick "fake" account. The intent isn't always malicious, for example, in 2015, Target announced it was planning on removing the gender descriptions from in-store signage within its children's toy sections. Many people flocked to the company's Facebook page to share their reactions to the news, it wasn't long before an account named "Ask ForHelp" with the Target logo as the profile picture started responding to unhappy customers with snarky, flippant remarks.
Turns out the account was created to appear as a Target customer service account, but it was, in fact, fake. Target responded to the internet troll by releasing an official statement outing the stunt as an incident facilitated by a fraudster.
However, scammers have been using brandjacking to facilitate their more malicious motives. At the start of the new year, Netflix has been at the center of a phishing scam much like the one I described before. An Australian cybersecurity firm is warning Netflix customers about a scam that informs users via email that their credit card no longer works.
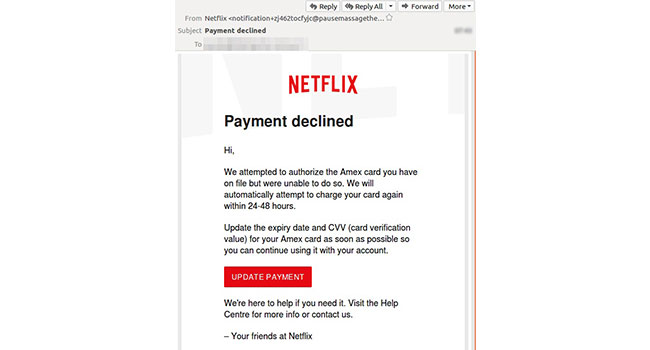
Mailguard issued the warning recently, reporting that the scammers are using "brandjacking" emails in order to get customers' credit card information. This isn't the first time Netflix has been targeted, a similar phishing scam popped up last Fall.
While their isn't really a way to "prevent" brandjacking from happening, businesses can be on their guard about possible scams including their brand names. The quicker a brand realizes they are being targeted and alerts their customers of the scheme, the worst the result for the scammer and the better the result for the company.
Consumers can also do their part to ensure they aren't the victim of a brandjacking phishing scam. Consumers should be wary of all emails that come to their accounts. If there is a problem with your payment on any of your online accounts, make sure you go straight to that website and check out the problem there. Do not click through the email to get to the account settings.
The FDA has a list of tips to avoid phishing scams, you can view them here.