
Cut & Paste to Digitally Streamlined Credentials
Using a robust, web-based ID software to create credentials with high-security features for a community’s public employees
Incorporated in 1979, the Town of Paradise, California is situated in the foothills of the Sierra Nevada Mountains, about 90 miles from the city of Sacramento. Like other cities and towns across the country, Paradise has its own dedicated Police Department.
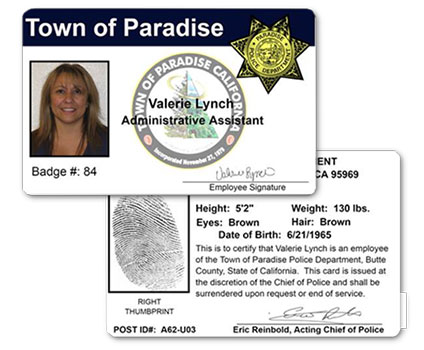
Paradise relies on their credential program to provide Town department employees with ID cards that offered a unified form of photo identification designed to authenticate badges and prevent fraudulent access. They also depend on their cards to verify their employment, status, and training ID number during on-site and o - site training. At the head of the program is Valerie Lynch, Paradise Police Department’s Administrative Assistant. Since 2001, Lynch has managed the Town’s credential program – from designing badges to printing them and finally distributing them to officials.
Find an Agile, Easy-to-Use ID Card Software Program Solution
When Lynch first began working at the department in 2001, she would run paper cards through a typewriter, take the employee’s photo with a film camera, pick up the photos at a local drug store, cut it out and glue the headshots onto the paper cards and manually laminate cards. “Using a typewriter, glue and laminate to make each of our ID cards was extremely time-consuming, sometimes messy and not at all convenient,” Lynch said.
When her department decided to digitize their ID card program as well as their card-making process with a plastic ID card printer in 2006, Lynch was delighted. She began researching online for reputable photo ID retailers who could make the transition smooth and streamlined. That’s when she found ID Wholesaler and ordered the department a Fargo C30e direct-to-card printer and entry-level software. It worked great for many years, but around 2015, it began to show its age.
Once again, Lynch was tasked with finding a new card printer. She decided they also needed an upgrade to their ID software that could accommodate multiple users at different locations across the police department’s network. Although the software she’d originally purchased with the C30e fit their business needs at the time, her card program now demanded more advanced features and capabilities. The next requirement was the software’s ability to integrate fingerprint and signature images into the design of the ID card. The final requirement was a software that was simple for users to learn and easy for them to create high-quality, professional-grade ID cards.
Integrate a Powerful & Secure Cloud-based ID Software
Lynch called her long-time ID Wholesaler Account Manager, Mathew Foss. He explained the features of the Magicard Rio Pro Printer and told her about a web-based software called CloudBadging.
He added that CloudBadging combines all the features and benefits of standard desktop ID card software into a cloud-based SaaS application (“Software as a Service”). It requires no installation and can be used virtually anywhere using a PC or Mac with internet access. Best of all, it came with a free subscription which allowed Lynch to “test drive” the software before purchasing it.
The free subscription allowed her to try the software and gain a better understanding of its features and capabilities. Most importantly, it was Lynch’s full responsibility to find a new software, so it was critical that it could manage the needs of the Paradise Police Department. Her reputation was riding on it.
Rely on the Expertise of a Leader
Asked whether she had any recommendations for someone looking to produce professional-quality ID cards, Lynch exclaimed, "Call ID Wholesaler…we had great success with them!"