25 Worst Passwords of All Time
To help you rule out the worst password ideas, FrontNet has put together a list of the 25 words passwords on the internet for 2018.
- By Jessica Davis
- Nov 13, 2018
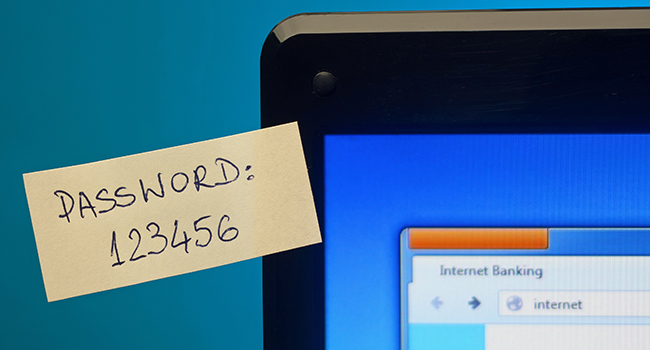
With data breaches so often dominating the cybersecurity news, we should be more conscious than ever about the strength of our passwords. No matter the account, your password needs to be as strong as possible to protect your private information.
To help you rule out the worst ideas, FrontNet has put together a list of the 25 words passwords on the internet for 2018. The list is as follows:
1. 123456
2. password
3. 12345678
4. qwerty
5. 12345
6. 123456789
7. football
8. 1234
9. 1234567
10. baseball
11. welcome
12. 1234567890
13. abc123
14. 111111
15. 1qaz2wsx
16. dragon
17. master
18. monkey
19. letmein
20. login
21. princess
22. qwertyuiop
23. solo
24. passw0rd
25. Starwars
It’s difficult to believe that anyone could be using “password” as their password in 2018, but unfortunately, this problem continues to plague us, especially as more work and interactions move online and we have to create accounts for more websites.
The best way to ensure password strength is to create long passwords with at least two or three different types of characters put in unpredictable places. You should also use a different password for every account you have, which means a password manager to keep track of your account credentials is a great idea.
For more information on protecting yourself from hacking attempts, see here. If you’ve already been hacked, here’s advice on what to do next.
About the Author
Jessica Davis is the Associate Content Editor for 1105 Media.