Army Considers More Multi-Factor Authentication Measures
The U.S. Army is working toward adding more authentication measures to provide more options to access Army online resources while maintaining information technology system security.
- By Jessica Davis
- Apr 24, 2019
The U.S. Army is working toward adding more authentication measures to provide more options to access Army online resources while maintaining information technology system security.
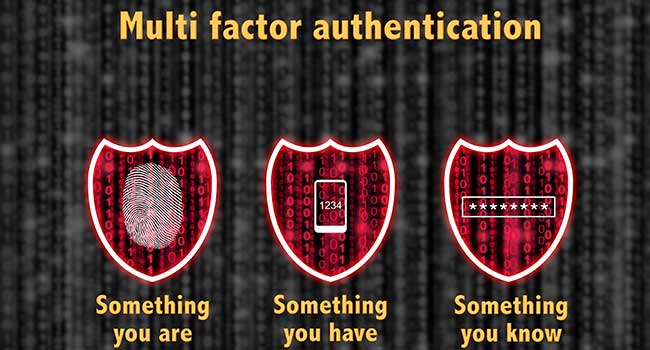
Army CIO/G-6 officials are working with Program Executive Office Enterprise Information Systems (PEO EIS) on alternatives to the Army’s current multi-factor authentication process (MFA). MFA requires users to present at least two points of verification across three categories—something you know, something you have, and something you are—to prove their identity, officials said.
"The commercial industry has seen that there's a greater need for protection, making sure the right people are accessing the right accounts," said Thaddeus Underwood, Identity Management and Communications Security division chief. "It makes sense that the Army is moving in the same direction. We are better protecting access to our IT networks to improve our cybersecurity posture by replacing username and password logins across the Army with MFA-secured options."
Currently, Army MFA measures require soldiers to use their Common Access Card (CAC) and personal id number to log into a government computer system, according to Underwood. However, because some of the Army currently serves in the Reserve or National Guard, not all soldiers have consistent access to government computer systems.
"You've got Reserve and National Guard members who only come to a government facility on the weekend for their drill training," Underwood said. "If there is online training that they need to do … they could potentially do that from home if they have a CAC and CAC reader," he said. "How do we provide them that level of access without having to use a CAC?"
The Army is currently considering two MFA alternatives: a mobile device app that allows for authentication, and a pre-registered USB-type device known as a Yubikey, Underwood said.
An authentication-type app would allow soldiers to access official sites without needing to use their CAC and reader. Theoretically, soldiers would download the app to their smartphone and register their phone online to link it to their Army identity, according to Underwood.
Once the app is registered, soldiers would log into official Army websites with their username and password, and the site would trigger a MFA process, sending a one-time-use passcode to their registered app. The soldier would then enter that passcode into the website and be authenticated for its use, able to access personnel records, online training and other resources without needing a CAC-enabled computer.
"We are at the final stages of developing the requirements. Next, we are going to ask commercial vendors to provide solution options," Underwood said. "We expect to have an initial-app prototype by this fall."
In addition to the app in development, PEO EIS is providing Yubikeys as an alternative method of MFA. A Yubikey is a registered USB-type device that can be inserted into a computers USB port, serving as a second form of authentication after the user logs into an official website, Uderwood said.
"The Yubikey solves the problem of not having a CAC and reader, but it doesn't solve needing a physical piece of equipment," Underwood said. "This device will probably be a better solution for some of our mission partners such as the American Red Cross, and first responders that act when an incident happens … and don't have a CAC to get access to our resources.”
Underwood said Yubikeys are currently undergoing integration testing by PEO EIS.
"Anytime you have new technology, you want to introduce it to existing technology and make sure that it will work," he said. "We expect user testing and field testing to begin in May."
About the Author
Jessica Davis is the Associate Content Editor for 1105 Media.