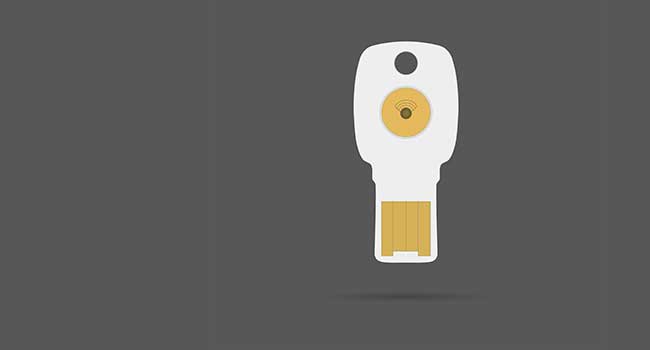
Google Replaces Titan Security Keys Due to Vulnerability
Google announced its Bluetooth security keys could be vulnerable to attack.
- By Sydny Shepard
- May 17, 2019
Google has discovered a security vulnerability so serious that it is telling users it will replace their Bluetooth Titan Security Keys for free.
In a press release, the company said that there is a "misconfiguration in the Titan Security Keys' Bluetooth pairing protocols" that could potentially allow an attacker to gain access to your account or device though some very specific circumstances.
One of the vulnerabilities described by Google allows an attacker within a 30-foot Bluetooth Low Energy range of your key when you press the button to authenticate a login, they could connect heir device to your security key. If they have your password, they could gain access to your account.
Another way a bad actor could make their way into your account is when you pair your device for the first time. An attacker could "masquerade as your affected security key and connect to your device," and then do the same things on your device that other Bluetooth devices can do, like act as a keyboard or a mouse.
Google has been leading the charge in two-factor authentication (2FA) for a long time now. It has been pushing its Titan Security Keys as a more secure way to enable 2FA than simply an authentication app, or SMS. Google is not wrong about trying to add another layer of security, but there is going to be a higher level of scrutiny on any potential vulnerabilities.
Google has made it know that if you have a "T1" or "T2" on your Titan Key, you are eligible for a replacement.
About the Author
Sydny Shepard is the Executive Editor of Campus Security & Life Safety.