Getting a Security Education at GSX
Seeing the technology and offerings first-hand was eye-opening at my first conference.
- By Haley Samsel
- Sep 12, 2019
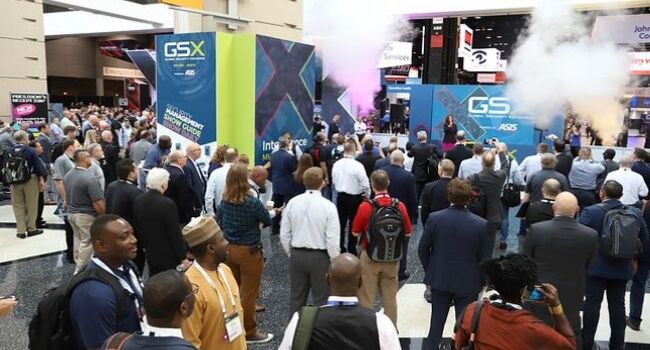
While the GSX conference has gotten smaller each year, my first one was the opposite of uneventful. I spent most of my days in Chicago on the exhibit floor, walking between the companies we covered for our Live From GSX 2019 program. In between stops, I had the chance to visit some of the other exhibitors and learn about their offerings in this rapidly changing industry.
As someone who has only written about security issues from a distance, it was fascinating to see how professionals approached the challenges we write about on a daily basis at Security Today. Among them is the upcoming government ban on federal contractors using Chinese video surveillance technology, which has posed strategic problems for companies large and small. I heard the topic brought up multiple times throughout GSX, and businesses offering video surveillance services are still moving to make sure they can meet the requirements.
In addition, I was eager to see how the cyber and physical security industries interacted at the conference. My main takeaway was that the two sectors are increasingly reliant on each other to ensure services like access control and video surveillance are not vulnerable to cyber threats.
That’s no surprise — experts have expressed similar views for years. But while there is increasing acknowledgment of this relationship, the two fields still feel a bit disconnected.
It’s admirable that physical security experts are willing to let cybersecurity pros take over when they’re not confident they can handle a customer’s need. However, there could be potentially negative consequences when people on the physical side don’t know the right questions to ask, or don’t recognize that a solution requires more stringent cybersecurity protection than usual. The same could be said of people on the cyber side who are not aware of how their solutions could be potentially burdensome (financially or otherwise) on consumers, dealers or integrators.
The best part of conferences like GSX is that they bring people from across this broad industry together to learn about their customer needs, but also the technology and challenges that their competitors are taking on. The education element, even outside of GSX’s speaker sessions, stood out to me — someone who is continuing to learn more about the industry day by day.
About the Author
Haley Samsel is an Associate Content Editor for the Infrastructure Solutions Group at 1105 Media.