Modernizing Data Distribution Capabilities
- By Scott Lucas
- May 11, 2021
Arizona-based Company Nurse has seen its share of faxes. So has everyone else in the workers’ compensation services industry. Reports and case documentation are still requested via fax or, increasingly, via email attachments.
In 2019, Henry Svendblad, Company Nurse CTO, decided the time was right to modernize the company’s data distribution capabilities, shifting from fax and email in favor of a modern APIs for the records his company managed and distributed. Along the way, he also aimed to establish Company Nurse as the undisputed leader in data privacy protection. Svendblad’s timing couldn’t have been better, and it’s an instructive tale of how an IT initiative can have a strategic business impact.
“Every customer conversation we were having included security and data privacy,” Svendblad said, “HIPAA has raised awareness and set the privacy bar for anyone handling patient information. But as it turns out, workers’ compensation isn’t regulated by HIPAA – and that’s led to some complacency in the industry. Our competitors just aren’t investing in data security.”
Svendblad envisioned a cloud-based approach to data collection that would do right by customers and position Company Nurse as the security leader at the same time.
Every company in the sector faces the risk of patient data loss. A successful breach could result in thousands of records, each containing personally identifiable information (PII), becoming public—or being used for identity theft or other cybercrimes. Beyond the direct impact on patients, breaches also raise the possibility of brand damage and costly remediation. The workers’ compensation process moves slowly so simply deleting older documents isn’t always an option – any solution would have to secure data no matter where it was stored or how it was collected.
Svendblad Got to Work
He planned to roll out the workers’ compensation industry’s first secure, cloud-based API solution for workers’ compensation injury reporting and triage while also enhancing safeguards around Company Nurse’s substantial trove of unstructured data. But applying data security policies to the faxes, reports, and documents in Company Nurse’s archives proved to be deceptively difficult. Security tools and techniques designed for databases don’t easily translate because unstructured data is hard to find and even harder to categorize, assess for risk and protect.
“We were making good progress on our cloud-based API solution, but unstructured data security was harder,” Svendblad said. “We wanted to go beyond typical folder-based access control to a true least-privileges model, where access depends on who needs it, not on where the file’s stored.”
While this would have been considered a nearly insurmountable challenge a few years ago, a new generation of data security tools, based on Artificial Intelligence (AI) and Natural Language Processing (NLP) is able to take on this type of use case with relative ease. These new tools are cloud-based, which simplifies implementation and lowers ongoing operational costs.
Each NLP- and AI-driven data security tool works slightly differently. One approach that is proving effective, however, involves autonomously grouping a company’s unstructured files into thematic clusters. Through NLP and AI, the solution can understand each document’s meaning and context. At that point, the solution is able to establish a security baseline for each cluster—encompassing factors such as sharing practices, content and context, file locations, access privilege configurations, group memberships, and more. It is possible to reveal risk – and configure access – by comparing each individual file’s security factors to the cluster’s baseline.
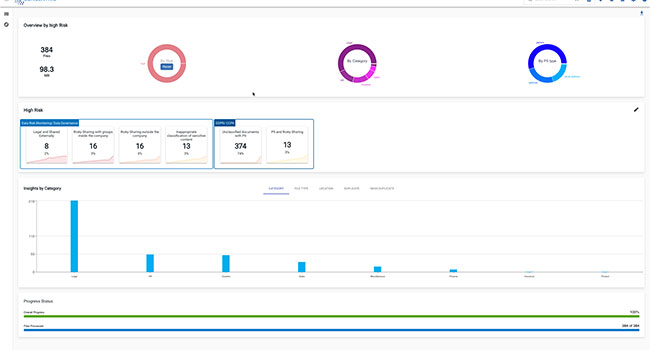
Company Nurse chose Concentric’s Semantic Intelligence solution to proactively mitigate its unstructured data risk exposure. In a matter of days, the solution completed a deep learning process to identify security weaknesses across the entire business. “We spotted areas for improvement right away,” Svendblad said. “We found a number of old reports on an out-of-the-way server and we identified some data that was overshared within Company Nurse. These weren’t data breaches, but by deleting the reports and tightening access permissions we substantially lowered our risk exposure.”
AI and NLP don’t solve unstructured data security problems by themselves, of course. It’s a policy-driven, organizational effort. Yet, without such new technologies, it is extremely difficult to discover risks in unstructured data and cost effectively devise a remediation process. Human-developed search rules and policies take months of effort to implement and leave behind substantial long-term maintenance burdens. Enlisting end-users to tag their content – another common approach – creates ongoing training and adoption barriers that often fail to provide the needed protection. AI can now do that work – accurately, autonomously and for a fraction of the cost.
Finding the right solution and then aligning it with security policies and practices are the keys to success in this area of data security work. Done right, this approach enables competitive advantage through stronger security and better protection of data. Today Company Nurse is the acknowledged sector leader in data security, recognized in a case study earning a Cloud Computing Excellence award earlier this year. Svendblad and his secure, cloud-based API solution are, at long last, on the verge of shedding faxes and eliminating email attachments forever.