Verizon recently released the 2020 Cyber Espionage Report (CER), their first-ever data-driven publication on advanced cyberattacks.

ZeroEyes, the only AI-based platform focused solely on weapons detection, has been selected by the Kenosha Unified School District (KUSD) of Wisconsin to help improve security on its campuses.
Keeping communities safe and secure with actionable, data-driven insights from advanced video analytics

Parks Associates recently released the new whitepaper “The Value of Professional Monitoring,”developed in cooperation with Rapid Response Monitoring, which finds the industry for professional monitoring grew by 5% from 2018 to 2019, a significant increase on a rate that had previously stayed flat.
ASIS International has announced the full slate of directors for its 2021 Global Board. The Global Board of Directors, first installed in 2020, is a major step in the association’s transition to a new global governance structure that allows ASIS to better provide service to its members at the local, regional, and global levels.
Nortek Control announced today the promotion of Jeff Shaw to senior director of product management.
Codelocks Inc. announces an ISO-certified photocatalytic coating which, when applied to Codelocks’ products, offers enhanced protection against viruses, bacteria, germs, volatile organic compounds (VOCs) and other environmental toxins.

Trend Micro Incorporated has identified a new class of cybercrime. Criminals are using cloud services and technology to speed up attacks, which decreases the amount of time enterprises have to identify and respond to a breach.
Concentric Inc. has announced the latest advancements available in its Semantic Intelligence data access governance solution that address the industry’s continued challenges with unstructured data security threats by autonomously identifying risk created by inappropriate access, sharing and management of unstructured data.

Reed Exhibitions and the Security Industry Association have just announced that ISC West 2021 is now being delayed until July 19-21.
- By Brent Dirks
- Nov 12, 2020
All young security professionals at Security Industry Association (SIA) member companies and SIA student members may earn one of five $3,000 SIA RISE Scholarships.
ADT Commercial continues its strategic M&A strategy, expanding its nationwide geographic footprint and deepening its capabilities to serve mid-market, national and large-scale commercial customers in New York and New Jersey with today’s announcement it has purchased Deterrent Technologies, Inc., based out of Ocean, NJ.
The NFL Players Association is looking into a complaint filed by New York Jets players about the presence of security cameras in the locker room at their training facility in Florham Park, N.J., a source close to the union confirmed to ESPN.
Here is a Q&A that answers questions about spoofing the voter. The answers come from Chris Krebbs, CISA director.
In an open letter to Twitter CEO Jack Dorsey, Department of Homeland Security (DHS) Acting Secretary Chad F. Wolf today called on Twitter to no longer obstruct Americans’ unalienable right to communicate with each other, their government, and its officials on the platform, because doing so endangers the national security.

The most recent elections is the most secure in the nation’s history. Or, is it? Government officials say it is the most secure ever.
ACRE has announced today the acquisition of Razberi Technologies based in Farmers Branch, Texas. This purchase will enhance ACRE’s strategic expansion plans for strengthening its video and communications business and product portfolio.
Houlton Station Border Patrol Agents and Border Patrol Explorer Post 1820 towed their Reconcraft 21’ RSDV boat down to Andy’s IGA in Houlton for the 2nd annual “Sink the Boat, Flood the Food Pantry” food drive on Oct. 31.

SIA recently submitted a letter to the Food and Drug Administration (FDA) Commissioner Stephen Hahn with a focus on an awareness that some companies are not following FDA guidelines related to the use of thermal imaging systems during the COVID-19 pandemic.

As we shop from the safety of our homes and fuel the digital economy, we expose ourselves to a great amount of risk, and fraudsters are taking advantage of this sharp increase in online shopping over the course of the COVID-19 crisis.
- By Thorsten Herbes
- Nov 02, 2020

To be successful in financial services, banks, investment firms and other institutions need to prove to their customer base that they are safe and trustworthy. Yet many still rely on passwords, PINs and other knowledge-based authentication factors—which are not only unreliable, but also insecure.
- By Simon Marchand
- Nov 02, 2020
EyeLock LLC recently announced that its award-winning software, EyeLock Identity Suite (EIS), now includes a Personal Identity Verification (PIV) credential format which is primarily used by the government to access federally-controlled facilities and information systems at the appropriate security level.
Johnson Controls is announcing the integration of its Tyco Software House C•CURE 9000 security and event management system with HID Global’s Origo® Mobile Identities and Seos® credential technology.
“Min Kang is an accomplished leader, with a proven track record in developing and implementing effective solutions to complex problems in the mobile industry,” said William E. Niles, CEO at Brinks Home Security.
SoFi Stadium, home to the Los Angeles Rams and Los Angeles Chargers and future site of Super Bowl LVI, 2023 College Football Championship, and the 2028 Olympics, just got a little safer.

The 2020 election season is a Big Deal as well it should be. The Vote, as foundational parts of the whole, is complicated in practice with history showing us just how complicated it can be. Protecting the process and making sure the Vote is fair, secure, and timely, is vital to American Democracy.
- By Saryu Nayyar
- Oct 28, 2020
Allied Universal® is pleased to announce that the North Carolina Rehabilitation Association selected the company for the Employer of the Year award in Charlotte, North Carolina.
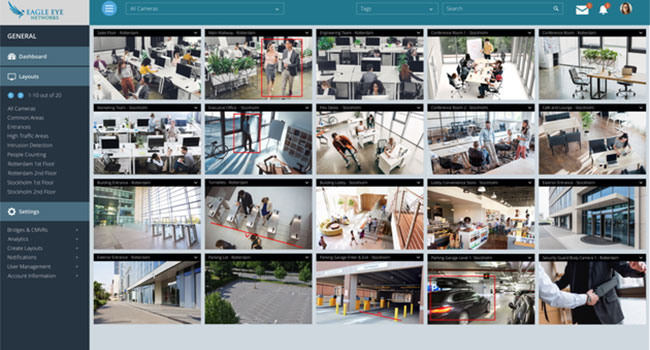
Eagle Eye Networks has raised $40 million of Series E funding from venture capital firm Accel (Facebook, Spotify, DocuSign) to continue its growth and expand its technology leadership.
- By Ralph C. Jensen
- Oct 27, 2020

To get excited about selling smaller surveillance projects at first thought is anti-intuitive. However, it may be best for the diversification and long-term growth for most integrators.
- By Robert Messer
- Oct 27, 2020

The American Crime Prevention Institute (ACPI) has developed a comprehensive training and education program designed as a vital step in strengthening community trust and respect for law enforcement.