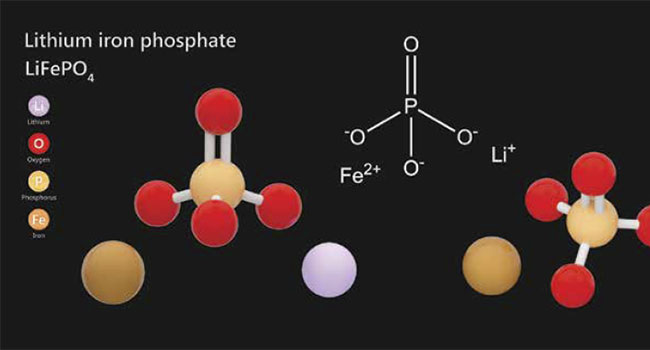
One of the primary criteria for any surveillance, access or security system is the requirement for a consistent and reliable power source, as even the most complex and expensive system solutions will be rendered useless if power is interrupted.
- By JR Andrews
- Apr 01, 2019

See no evil, hear no evil, speak no evil: It is tempting for physical security professionals to take this passive approach to cybersecurity.
- By Tom Galvin
- Apr 01, 2019

As cybercrime continues to plague companies of all sizes, across all industries both public and private, we wanted to take this opportunity to explore options that can help protect your data and your business.
- By Rich Aycock
- Apr 01, 2019

The breach exposed diagnostic results, healthcare numbers and personal contact information.
- By Sydny Shepard
- Mar 29, 2019

Everyone should be changing their Facebook passwords after it was discovered all use passwords have been left unencrypted and searchable in plaintext.

2FA is more secure than single-factor methods only requiring a password, but it's not an impenetrable method.
- By Kayla Matthews
- Mar 25, 2019

DNS leaks can be a surprisingly common issue and are often only noticed when actively looked for.

Facebook stored “hundreds of millions” of account passwords unencrypted and viewable as plain text to tens of thousands of company employees, KrebsonSecurity reported Thursday.
- By Jessica Davis
- Mar 22, 2019

Since each insider threat is very different, preventing them is challenging.
- By Tim Matthews
- Mar 19, 2019

What does the future hold for audit and compliance?
- By Simon Hill
- Mar 18, 2019

Despite their new image as a failed cybersecurity company, Equifax is warning Canadians to do more to protect their data.
- By Sydny Shepard
- Mar 15, 2019

A survey found that security professionals are making the move to biometrics, but that they could be doing more to protect data.
- By Sydny Shepard
- Mar 15, 2019
The Internet of Things Cybersecurity Improvement Act aims to establish a bare minimum of security standards for IoT devices used by the federal government
- By Jessica Davis
- Mar 13, 2019

Vulnerabilities found in two different car alarms left three million vehicles susceptible to hijack globally.
- By Sydny Shepard
- Mar 11, 2019
Machine learning and Twitter could be the future of catching security flaws and vulnerabilities early.
- By Sydny Shepard
- Mar 11, 2019

“I believe the future of communication will increasingly shift to private, encrypted services where people can be confident what they say to each other stays secure and their messages and content won't stick around forever. This is the future I hope we will help bring about,” Zuckerberg wrote.
- By Jessica Davis
- Mar 08, 2019

Google has discovered a Zero-Day Vulnerability [CVE-2019-5786] that is being exploited by bad actors. If you are a Chrome user, you are at risk. Make sure your browser has been updated to the latest patched version [72.0.3626.121], which fixes the vulnerability.
- By Susan Alexandra
- Mar 08, 2019

The cyberattacks focused on universities that either studied underwater technology or had faculty with relevant backgrounds, according to reports.
- By Jessica Davis
- Mar 07, 2019

Verizon takes its Data Breach Investigations Report and refocuses on Insider Threat reports.
- By Sydny Shepard
- Mar 06, 2019

Facebook users have found that a phone number they added to their account for the sole purpose of two-factor authentication can be used to look up their account by advertisers and strangers.
- By Sydny Shepard
- Mar 06, 2019