
The health organization realized during an investigation of an August breach that its systems had been breached several times prior to the known attack.
- By Haley Samsel
- Oct 14, 2019

The massive MegaFace dataset may have violated the Illinois Biometric Information Privacy Act, a 2008 law that protects residents from using facial scans without their permission.
- By Haley Samsel
- Oct 14, 2019

For the third year in a row, SMBs are reporting big increases in the frequency of cybersecurity attacks.
- By Haley Samsel
- Oct 11, 2019

Law enforcement are increasingly worried about the possibility of end-to-end encryption, which does not provide police with a way to access communications between potential suspects.
- By Haley Samsel
- Oct 08, 2019

Over 200 accounts were targeted by the group of hackers, but only four were compromised, according to Microsoft.
- By Haley Samsel
- Oct 07, 2019

Even if an organization decides to pay a ransom against the FBI’s advice, they should report the crime to law enforcement, according to the FBI alert.
- By Haley Samsel
- Oct 07, 2019

In the latest ransomware attack scourge, three hospitals in Alabama were able to continue serving existing patients but said they could not take new cases.
- By Haley Samsel
- Oct 04, 2019
Recent hacks into databases of some of the world’s biggest corporations and government organizations put the personal information of billions of people at risk.
- By Mohammed Murad
- Oct 01, 2019

Privacy issues continue to dominate headlines as the world’s biggest companies are being challenged on the ways they collect and use people’s data. Consumers are growing more concerned about how their activities are being tracked across the web as companies sell information to advertisers for a profit.
- By Neil Huntingdon
- Oct 01, 2019
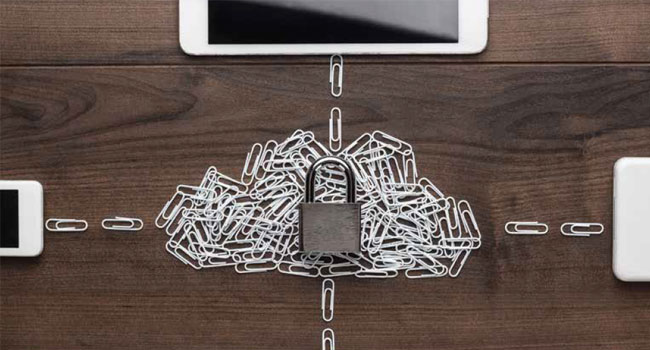
Cloud storage is most used by small-and-medium businesses (SMBs). The reason is that it comes with many benefits for organizations in terms of flexibility and more importantly productivity.
- By François Amigorena
- Oct 01, 2019

4.9 million users have been affected by the data breach, which DoorDash discovered in the past month.
- By Haley Samsel
- Sep 30, 2019

The company originally planned to phase out security patches for Windows 7 in January. Now, Microsoft will continue issuing free updates for election systems around the world.
- By Haley Samsel
- Sep 24, 2019

The fight over increased funding for election security is far from over, though: The House and Senate still need to agree on a number for the final version of the bill.
- By Haley Samsel
- Sep 23, 2019

A new investigation discovered that the medical images and health data of more than 5 million patients in the U.S. was readily accessible on the web without a password or login.
- By Haley Samsel
- Sep 18, 2019

The department announced the sanctions Friday after it said that North Korean intelligence groups targeted American critical infrastructure, particularly the financial system.
- By Haley Samsel
- Sep 17, 2019

Phishing scams continues to be a widespread problem for businesses and individuals alike. But there are several ways to recognize that you could be getting scammed.
- By Susan Alexandra
- Sep 09, 2019

A database that was left without password protection was discovered by a security researcher, who said 419 million records of Facebook user phone numbers were exposed.
- By Haley Samsel
- Sep 06, 2019

Information mishandling, snooping and location tracking are often the ways in which users find their privacy violated online.
- By Susan Alexandra
- Sep 03, 2019

The number and breadth of devices that make up the Internet of Things (IoT) continues to grow rapidly, with everything from kitchen appliances to video surveillance and access control systems offering the ability to connect to a network.
- By Ryan Zatolokin
- Sep 01, 2019

We know by now that there is an abundance of business advantages in the cloud — it’s agile and cost-efficient, and, with little to no hardware maintenance, it’s easier to update and perform maintenance on than traditional on-site servers.