
IN FORCE 911 allows staff to quickly launch an emergency alert and facilitates quick communication between victims and police.
- By Haley Samsel
- Jul 16, 2019

Respondents, who answered 22 percent of questions incorrectly, struggled most with assessments about mobile device encryption and protections for personally identifiable information.
- By Haley Samsel
- Jul 11, 2019

The application is the Chinese government’s latest escalation of its surveillance operation of Uighurs, a Muslim minority, for supposed terrorist activity.
- By Haley Samsel
- Jul 08, 2019

Regardless of size or business type, companies must institute these basic practices to make sure their organizations are well protected from cybercriminals.
- By Susan Alexandra
- Jul 05, 2019

A now-discontinued smart home hub had flaws that allowed researchers to hack into the device without even knowing the plain-text password put in place by the owner.
- By Haley Samsel
- Jul 05, 2019

Researchers have found over 2,000 apps that are potentially counterfeits, modeled after popular app downloads. These counterfeits contain harmful malware that could harm unsuspecting users.
- By Kaitlyn DeHaven
- Jun 28, 2019

Germany has decided to level the playing field and offer all foreign companies fair and equal chances to build the national 5G infrastructure. Huawei has responded, claiming that despite the warnings of the United States, they will be able to comply and meet these standards.
- By Kaitlyn DeHaven
- Jun 26, 2019

After a major telephone outage in the Netherlands took down the nation’s emergency phone number yesterday, police forces took the streets to ensure people could contact emergency services through them.
- By Kaitlyn DeHaven
- Jun 25, 2019

An DDoS attack aimed at slowing connectivity for the Telegram app took place this week. The cyberattack coincided with large protests in Hong Kong, and with most of the IP addresses coming from China, it is speculated that they were involved in the attack.
- By Kaitlyn DeHaven
- Jun 14, 2019

Apple has “you control your data" for a while now, but with these new updates, the data is almost completely the consumers’.
- By Kaitlyn DeHaven
- Jun 06, 2019

Here's what you need to know about WhatsApp's major security flaw.
- By Sydny Shepard
- May 16, 2019

The tenth version of Android will include finer control over privacy and improvements to Android security updates, Google announced Tuesday at its I/O 2019 event
- By Jessica Davis
- May 08, 2019

Chicago Metropolitan Metra transportation system launches a smartphone security app to report safety concerns.
- By Sydny Shepard
- Apr 22, 2019

Lyft has announced two new features to enhance the security and safety of the riders using the Lyft platform.
- By Sydny Shepard
- Apr 18, 2019

There are several things riders can and should do before and during a ride to take charge of their own security and make sure that the vehicle is one they have booked.
- By Matthew Bradley
- Apr 15, 2019

Apple has announced massive security fixes in new iOS 12.2.
- By Sydny Shepard
- Mar 28, 2019

5G is the talk of the town, but is it free of security risks?
- By Sydny Shepard
- Feb 27, 2019

An investigation by Motherboard has found that an estimated 250 bounty hunters and related businesses had access to customer location data from AT&T, T-Mobile and Sprint.
- By Jessica Davis
- Feb 12, 2019
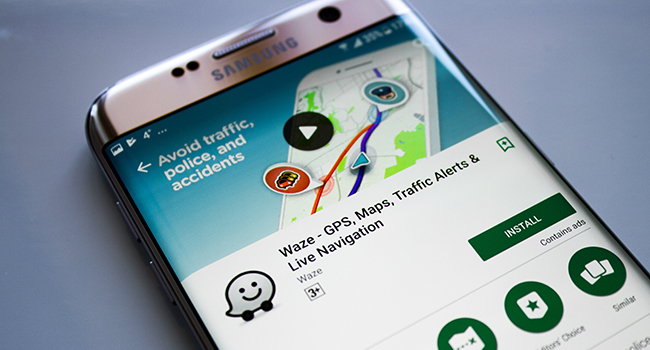
"Individuals who post the locations of DWI checkpoints may be engaging in criminal conduct since such actions could be intentional attempts to prevent and/or impair the administration of the DWI laws and other relevant criminal and traffic laws,” wrote NYPD acting Deputy Commissioner Ann Prunty in a Feb. 2 letter to Google.
- By Jessica Davis
- Feb 11, 2019

Apple is telling app developers to either remove or properly disclose to users their use of code that allows them to record the way a user interacts with their iPhone apps—or face removal from the app store.
- By Jessica Davis
- Feb 11, 2019