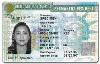
Latest Generation of Green Cards Among Most Secure IDs Worldwide
- By Laura Williams
- Mar 07, 2011
Organizations often take one of two approaches to security: reactionary, acting after a crisis to patch a hole, or proactive, taking preventive action before a problem trips them up.
When the U.S. Citizenship and Immigration Services (CIS) last year upgraded the technology in its permanent resident cards, colloquially called "green cards," it took the second path.
“We do not have problems with the old one, but we didn’t want to wait until we had problems; we wanted to stay ahead of any problems,” said Sandra Landis, chief of the integrated document production division at CIS. “It’s always prudent to upgrade the security features of documents that have a long lifecycle in circulation.”
The approximately 750,000 cards issued between 1979 and 1989 have no expiration date, and the generation of cards after that expires after 10 years, making green cards one of the longest-circulating identity documents in the country. According to Lasercard, the company that has manufactured the card’s base component for 14 years, CIS orders between 1.8 and 2 million cards per year.
The new cards, which began circulating in May 2010, boast visual, physical and digital security features, including optical security media (OSM) from Lasercard and an RFID tag. Indeed, just two months after its release, Frost and Sullivan placed the U.S. green card at the top of the list of the most secure government-based identity documents. Report authors described the upgraded card as “among the most physically secure and counterfeit-resistant machine-readable identification cards ever issued.”
The OSM itself has three layers of data protection. The visual level consists of high-resolution security images printed at 24,000 dpi (the average magazine is printed at 300 dpi). This level of detail makes it "virtually impossible for criminals to copy without having access to millions of dollars of printing equipment," according to Stephen Price-Francis, Lasercard’s vice president of marketing. It also has a personalized embedded hologram that consists of a laser-etched likeness of the cardholder and some biographical information, such as name, gender and card expiration date. Finally, the OSM contains a hidden image that an inspector can reveal only with a laser light.
The card itself has a second-generation RFID tag that can be read from up to 30 feet away. When sensors at a border crossing detect the presence of the tag, they automatically begin the process of bringing up a cardholder’s file, which makes the border-crossing process more efficient.
The results of the past year testify to the card’s high level of security. Landis said that Immigration and Customs Enforcement, the department that handles the enforcement aspect of the green card program, has yet to detect any attempts at counterfeiting the cards. According to Price-Francis, counterfeiters would have to make a significant capital investment in a multi-year research and development program to come even close to reproducing the card. Instead, said Landis, counterfeiters are focusing their efforts on less-secure generations of cards that were issued before the previous generation.
And the final change CIS made to the card? It’s color. The card had been white but is now green, meaning it once again lives up to its name: The nickname came about in the early years of the program, when cards were actually green. Between 1964 and 2010, though, they sported a variety of colors, including pink and blue.
About the Author
Laura Williams is content development editor for Security Products magazine.