
The Seizure of American Phone Records
- By Ginger Hill
- Jun 06, 2013
Be careful who you’re calling on your smartphone because these details, and more, may be handed over to authorities.
 Since April 25, 2013, U.S. authorities have been seizing call detail records and telephony meta data from Verizon Business Network Services, fulfilling a top-secret order that was filed by the FBI. A judge of the U.S. Foreign Intelligence Court signed the order, authorized by the Patriot Act that enables the National Security Agency to obtain phone numbers, location, time and duration of calls from any of the Verizon conglomerate’s 121 million customer accounts. Supported by the order, authorities will be able to seize call detail records for approximately 3 months, concluding on July 19, 2013.
Since April 25, 2013, U.S. authorities have been seizing call detail records and telephony meta data from Verizon Business Network Services, fulfilling a top-secret order that was filed by the FBI. A judge of the U.S. Foreign Intelligence Court signed the order, authorized by the Patriot Act that enables the National Security Agency to obtain phone numbers, location, time and duration of calls from any of the Verizon conglomerate’s 121 million customer accounts. Supported by the order, authorities will be able to seize call detail records for approximately 3 months, concluding on July 19, 2013.
But, why is this happening? Apparently authorities are worried about domestic surveillance in the U.S. related to terrorism and terrorist plots, although no statements have yet been released.
 It’s also interesting to note that this type of situation actually came up during the Bush administration, but this is the first time in connection with the Obama Administration.
It’s also interesting to note that this type of situation actually came up during the Bush administration, but this is the first time in connection with the Obama Administration.
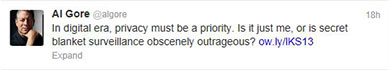
As we await the much anticipated comments of a classified briefing, groups and individuals are speaking out. Activist groups that protect privacy are concerned that Verizon is not doing enough to safeguard their customer’s information. While some Democrats are appalled at the seizure (see Vice President Al Gore’s Tweet), some Republicans are in favor of the order. Still others, like the American Civil Liberties Union, call for an immediate end to the order followed by a congressional investigation.
My opinion? If you’re not doing something wrong in the first place, then you have nothing to worry about. Anything the U.S. can do to protect us from terrorism, I’m all for it.
Source: http://www.cnn.com/2013/06/06/politics/nsa-verizon-records/index.html?hpt=hp_t2
About the Author
Ginger Hill is Group Social Media Manager.