 Alright iPhone fans! It’s the day we’ve all been waiting for: the unveiling of the iPhone 5s! In my opinion, it has a sleek and modern design, but according to Apple, and I suppose as with all relationships, it’s what’s on the inside that counts.
Alright iPhone fans! It’s the day we’ve all been waiting for: the unveiling of the iPhone 5s! In my opinion, it has a sleek and modern design, but according to Apple, and I suppose as with all relationships, it’s what’s on the inside that counts.
“Every single component, every process has been considered and measured to make sure that it’s truly useful and that it actually enhances the user’s experience,” explained Senior Vice President of Design, Jony Ive.
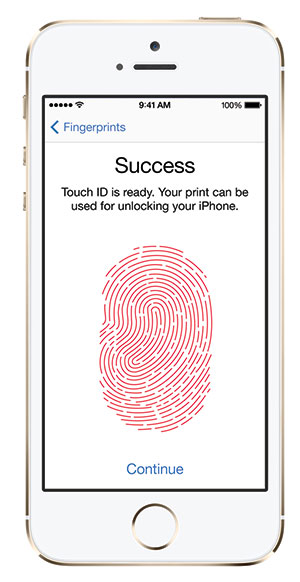
Apple wanted to offer iPhone users a way to protect all their important data that they carry around with them on a daily basis. So, just what is the best way to provide iPhone security? Apple figures with biometrics, the use of the fingerprint. Hence, the creation of Touch ID.
“Your fingerprint is one of the best passwords in the world. It’s always with you, and no two are exactly alike, so it made perfect sense to create a simple, seamless way to use it as a password,” confirmed Senior Vice President, Hardware Engineering, Dan Riccio.
Touch ID is very user-friendly and each time it’s used, it gets better at reading the user’s fingerprint based on the three classes of fingerprints: arch, loop and whorl.
Let’s explore Touch ID a little further.
Touch ID Technology
- Sapphire Crystal: one of the clearest, hardest materials available to protect the sensor and acts as a lens to precisely focus on the user’s finger.
- Steel Ring: surrounds the sapphire crystal and detects the user’s finger, then communicates with Touch ID, telling it to start reading the fingerprint.
- Advanced Capacitive Touch: takes high-resolution image of the user’s fingerprint from the sub-epidermal layers of the skin.
How Touch ID Works
- Touch the home button;
- Touch ID sensor reads user’s fingerprint;
- iPhone 5 s automatically unlocks.
Unique Touch ID Characteristics
- Can authorize purchases from iPhone 5 s;
- Able to read multiple fingerprints in any orientation;
- Maps individual ridges of user’s fingerprint;
- Inspects minor variations in ridge direction caused by pores;
- Encrypts all fingerprint information;
- A7 chip – stores fingerprint information, locking it away.
Apple takes pride in “making something as security so effortless and so simple,” said Ive. “We believe that the technology at it’s very best, at its most empowering when it simply disappears.”
Guess there IS some magic in the art of disappearing?
Sources: http://www.imore.com/apple-announces-touch-id-fingerprint-sensor-iphone-5s?utm_source=dlvr.it&utm_medium=twitter
http://www.theverge.com/2013/9/10/4715372/confirmed-apple-iphone-5s-will-include-touch-id-fingerprint-scanner
http://www.apple.com/iphone-5s/videos/#video-touch