To assist businesses in managing the growing risk of web-based attacks, the National Institute for Standards and Technology has assembled a 41-page cybersecurity framework as a guide for cybersecurity. Broken into 4 different tiers of protection according to varying risks and resources and introduced by the White House earlier today, President Obama signed the official order for this framework earlier this month.
“We cannot look back years from now and wonder why we did nothing in the fact of real threats to our security and our economy,” said Obama.
Below is the Framework Core, comprised of 4 elements that present key cybersecurity outcomes identified by specific industries. For the security industry, I think it would be beneficial to complete this core for as many verticals as possible, from education to oil and gas to fire and life safety to access control and beyond.
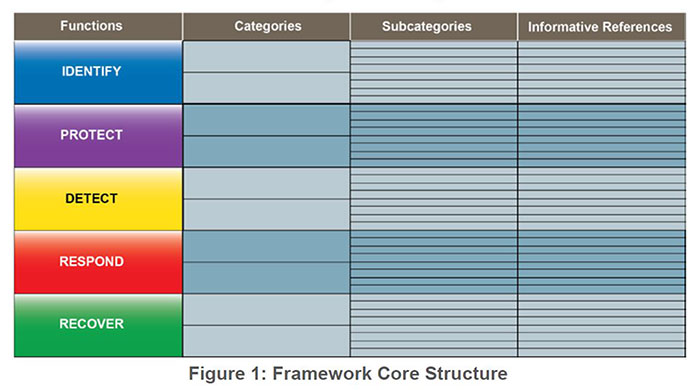
Functions Column – organizes basic cyber security activities; aids organizations in managing risk; addresses threats; and improves learning from previous activities.
Identify: manage cybersecurity risks by understanding business context, identifying resources used to support the business; creating risk management strategy.
Protect: implement safeguards to limit and/or contain the impact of unwanted cyber events.
Detect: implement activities to ensure a timely discover of unwanted cyber events.
Respond: take action quickly and effectively.
Recover: develop and implement a plan for resiliency and to restore business functions quickly.
Categories Column – groups of cybersecurity outcomes closely tied to particular activities.
Subcategories Column – specific outcomes of management activities.
Informative References Column – standards, guidelines and practices.
Once you have identified your company’s framework, it’s time to discover how your organization views cybersecurity risks and identify the processes in place to manage these risks by choosing the tier in which your business currently identifies with most.
Click here for Part 2 of this article where I introduce the tiers and give tips on how to select the correct tier for your company!
(Image from the official framework's PDF.)