IT Security Compliance for Cloud Service Providers
- By Gábor Marosvári
- Aug 01, 2014
 Compliance with increasingly stringent regulations
for organizations providing outsourced IT
services, particularly in regards to data protection,
is becoming more difficult. Reputation and
client trust are fragile assets, and compliance
with industry standards and legal regulations is
essential to earn and maintain them. Cloud service providers (CSP)
consider compliance a magical term: on one hand it’s critical to
their success; on the other hand it’s imposing time-consuming
burdens on the business.
Compliance with increasingly stringent regulations
for organizations providing outsourced IT
services, particularly in regards to data protection,
is becoming more difficult. Reputation and
client trust are fragile assets, and compliance
with industry standards and legal regulations is
essential to earn and maintain them. Cloud service providers (CSP)
consider compliance a magical term: on one hand it’s critical to
their success; on the other hand it’s imposing time-consuming
burdens on the business.
A special area of compliance is IT security compliance, which
is based on legal provisions and international standards. Geographic
borders become blurred, however, in the provision of
cloud services, making it impossible to regulate the sector solely
based on local regulations. This calls for international IT security
standards, such as PCI-DSS, ISO:27001, or SSAE 16/ISAE 3402
(formerly SAS 70). The largest CSPs such as Amazon Web Services
and Microsoft Azure strengthen their customers’ trust by
meeting these standards.
The standards include a broad range of requirements that require
a comprehensive approach to compliance. In each instance,
CSPs need to understand and interpret the requirements from
their own perspective, then enact a thorough implementation
program. This includes meeting certain requirements with specialized
software. Privileged access management and centralized
log management are areas in which software is typically used to
meet compliance requirements, and can lead to significant cost
reductions, as well as an increased level of security.
The Current Market Landscape
Among Cloud Providers
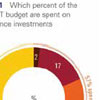
Which percent of their yearly IT budget is spent on compliance
investments? What is their primary motivation to meet regulations?
Which are the most important industry regulations they
need to meet? Which are the most important control areas when
talking about compliance strategy? What type of users’s activities
should be primarily monitored in cloud environments? How
matured are the Privileged User’s Management strategies at
cloud providers?
BalaBit IT Security and KPMG in Hungary jointly conducted
an international market survey1 titled “Compliance in the IT Service
Provider Sector”. The research involved 120 IT directors of
IT and cloud service providers, and was conducted in February.
Figure 1 shows that approximately 60 percent of service providers
spend more than 10 percent of their annual IT budget on
investments related to IT security compliance. Moreover, almost
one out of five spends more
than 20 percent of their annual
budget on compliance
related items, which is well
above the industry average.
More than two-thirds
of those surveyed use compliance
with standards
primarily to ensure secure
operations. This result is
a positive development, as
it indicates that most IT
cloud service providers regard
industry regulations
as a framework for developing
their companies’ risk
management practices.
The vast majority of respondents
use compliance
for maintaining their reputation
and acquiring more
customers, which clearly shows that service providers see compliance
as crucial to building trust.
Results of the survey also showed that most IT service providers
consider compliance with the international standards (for
example, ISO 27001 and PCI DSS) important. Naturally, the data
protection regulations of the countries where a given service providers’
data centers reside are important. It is, however, essential
to note that legal regulations usually build upon the principles of
some international standard.
It turns out that (privileged) user access control and log management
are critical elements of service providers’ compliance
strategies, whereas basic technologies such as antivirus and firewall
systems are much less important.
For the majority of respondents (57 percent), monitoring internal
and external access to cloud infrastructure is equally important.
This can be explained by the fact that access monitoring
systems provide strong evidence for service providers in disputes
with their customers and can settle differences of opinion quickly
and cost-effectively.
It is clear from our research that most service providers employ
generic user management and various levels of authorization
and authentication systems. However, only 42 percent of
respondents monitor and audit privileged users’ activity. Without
the right auditing tool, it is impossible to definitively determine
“who did what” in a given network, which can lead to disputes
over responsibility and costly investigations.
This article originally appeared in the August 2014 issue of Security Today.