Sorority Sisters Feel Patronized about Ban
- By Ginger Hill
- Feb 02, 2015
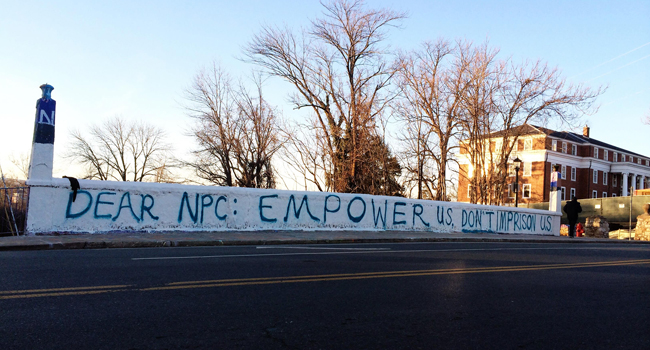
The “request” came in the form of a written letter, with penalties for non-compliance, from the national presidents of the 16 sororities represented on the University of Virginia’s campus. This document encouraged sorority members not to participate in fraternity’s “Boy’s Bid Night” activities and to plan “sisterhood events” instead to protect their “safety and well-being.” Even though they followed the rules not to participate in fraternity activities, sorority sisters at the University of Virginia weren’t the least bit happy about it.
Some sorority members felt this request treated them as “untrustworthy,” while others took a more proactive stance against the letter. Erin Dryer, a third year student and sorority member was one such student. She wrote an article to the Washington Post, emphasizing that this request was demeaning, discouraging and ineffective.
“If our only solution [for sexual assault] is to tell women to stay inside their homes and not associate with any of their male Greek [meaning fraternity members] friends, then I think that is discouraging and we are setting a terrible example for colleges across America,” said Dryer.
This decision was made without any student input and seems to identify men as dangerous and women as powerless.
I can understand how the national sorority presidents want to protect their sorority members; however, it does paint a very discouraging picture of let the boys be boys while the girls stay at home. When it comes to assault of any kind, it’s everybody’s job to fight against this horrific act, male and female.
What do you think readers?
- Do you agree with what the national presidents requested of sorority members?
- Do you think it was fair to “request” this and then threaten sororities with penalties for non-compliance?
- Do you think students, both male and female, should have had a say in this decision?
As always, looking forward to your reactions, thoughts and opinions.
Image from NBC News.
About the Author
Ginger Hill is Group Social Media Manager.