Security Issues Created by What a Computer 'Sees'
- By Ginger Hill
- Mar 25, 2015
It’s amazing how computers are learning to recognize objects almost with human ability, but these machines can be fooled by optical illusions according to Cornell researchers at the University of Wyoming Evolving Artificial Intelligence Laboratory. This, of course, raises security concerns.
Researchers created images that look like white noise or random patterns to the human eye where as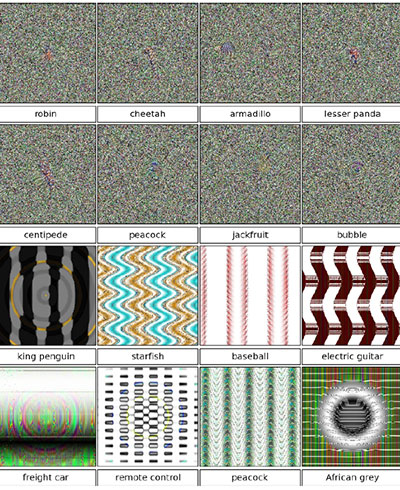 computers have the ability to identify them as common objects. Through training, computers are shown photos of objects from many different views along with the name of the object associated with it in human vocabulary. As a computer “looks” at the photos, it assembles a model that fits them all and will “learn” to match a new photo of the same object. However, it’s during training that security can become an issue.
computers have the ability to identify them as common objects. Through training, computers are shown photos of objects from many different views along with the name of the object associated with it in human vocabulary. As a computer “looks” at the photos, it assembles a model that fits them all and will “learn” to match a new photo of the same object. However, it’s during training that security can become an issue.
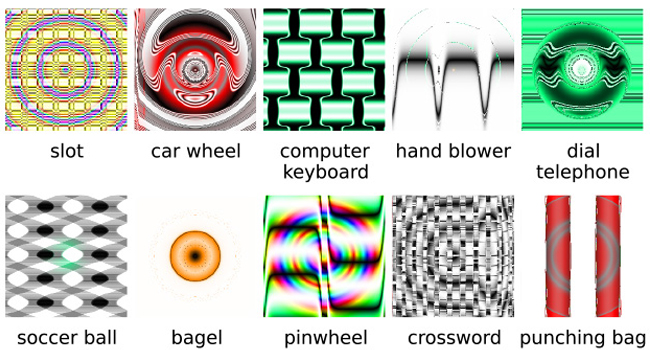
Researchers in the Cornell Creative Machines lab started training a computer to recognize an image, but with a twist. They slowly integrated mutated views of the image until eventually the original image was unrecognizable with the human eye, yet the computer was still able to recognize the original image with over 99% accuracy. This test proved that it’s possible to fool a computer into learning something that is not true. Because of this, malicious web pages could include fake images to fool search engines; fake images could be used to bypass safe search filters; or an abstract image may be accepted by a facial recognition system as an authorized visitor.
Image from: http://news.cornell.edu/stories/2015/03/images-fool-computer-vision-raise-security-concerns
About the Author
Ginger Hill is Group Social Media Manager.