Study: Police Usage of Facial Recognition Technology is Unregulated
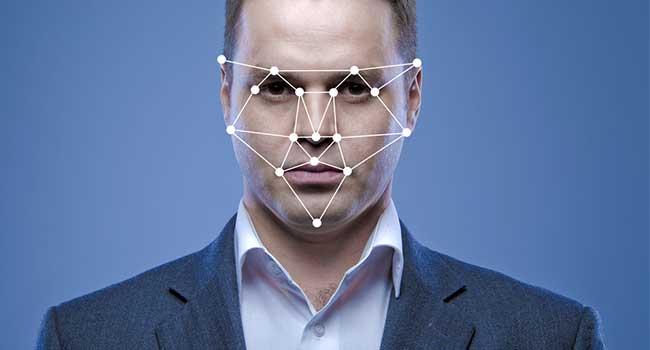
If you live in the United States, there is a 50 percent chance that your photo is in a facial recognition database used by your state’s law enforcement.
A study by Georgetown Law’s Center of Privacy & Technology shows that most people don’t know that their photo is being used in a facial recognition database that, according to the study, is generally unregulated. Altogether, more than 117 million American adults are subject to face-scanning systems.
The year-long investigation found that police departments in nearly half of the U.S. states can use facial recognition software to compare surveillance images with databases of ID photos or mugshots. While some departments only use facial recognition to confirm the identity of a suspect who has been detained, others continuously analyze footage from surveillance cameras to determine exactly who is walking by at any particular moment.
The authors of the piece, Clare Garvie, Alvaro Bedoya and Jonathan Frankle, contend that facial recognition is fundamentally different from other types of searches because it makes it easy for police to track people by their physical features, rather than by keeping an eye on their possessions and technology.
The technology allows officers to track large groups of people who aren’t even suspected of committing a crime.
Courts have yet to determine if facial recognition is a type of “search,” which would limit its use under the Fourth Amendment; so many departments use it on the public indiscriminately. Many of the states that have access to a facial recognition database only do a few checks on how they used them. Only five states have any laws that touch on how law enforcement can use facial recognition, and none of them take on more than one aspect of the issue.
Because the use of facial recognition is so heavy under regulated, law enforcement agencies have gotten away with some pretty absurd uses of the technology. For example, the study explained an event in Maricopa County, Arizona, where the sheriff’s office downloaded every driver’s license and mugshot from every resident of Honduras, provided by the Honduran government, to its facial recognition database.
In contrast to the absurd findings, the study also pointed out police departments that were using facial recognition databases “responsibly,” such as the Seattle Police Department that banned real-time facial recognition and consulted the American Civil Liberties Union when developing its policy for the technology.
Still, most departments that implement some sort of facial recognition have no limits on how often, when and on who their technology is used on. The authors hope to push more law enforcement on the technology and move agencies toward more transparency.