We See You
Do you know who’s lurking beyond your cameras?
- By Robert Jones
- Aug 01, 2017
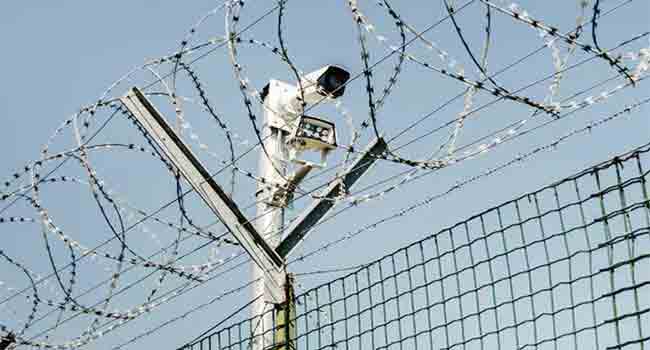
The last major advancement in commercial perimeter
security was the introduction of CCTV cameras. While
this technology addressed some of the surveillance
needs associated with facility protection, it failed to
fully address the challenges posed by threats outside of
your immediate view.
Today, we continue to guard our facilities with fences, cameras,
and access control systems, a growing market anticipated to be valued
at $37.43 billion by the year 2021. But does this anticipated investment
make sense, and does it really equate to better security than
we currently have today?
The answer is no because current protection strategies focus too
heavily on protecting a facility’s physical perimeter rather than protecting
the facility itself. Until the industry alters course, money will
continue to be wasted and vulnerabilities will continue to be exploited.
Securing a perimeter is about more than just the physical boundaries
of your facility or asset. It means effectively being able to detect
threat activity early enough to allow an effective response before you
are at risk of suffering loss.
Traditional perimeter security measures are reactive, not proactive,
which results in a rushed and ineffective threat response. While
these solutions play an important role in defense, they are insufficient
and must be augmented with other systems to improve their overall
efficiency and effectiveness.
Thinking Ahead
A select number of organizations are beginning to think ahead and implement
these proactive solutions. Less attention is being given to the
latest and greatest technology, and more energy is being spent developing
a security plan that provides an advance warning of threat activity.
The perimeter intrusion detection systems market, a subset of the
larger physical security industry, is seeing continued growth as a result.
It’s forecasted to reach $5.82 billion by 2021 with a compound annual
growth rate of 7.1 percent over the 5 year period following 2016.
Driving factors for this transition include a growing risk of terrorism,
continued problems with immigration, increased government
regulation, advancements in video surveillance technology, and a desire
to reduce the amount of man-hours needed for security. Traditionally,
false alarm rates have been a limitation to the adoption of
these intrusion detection systems but new technology is emerging to
counter these perceptions.
While many security professionals are looking to adopt a more
proactive security plan, there are countless organizations still caught
in the past who should be rethinking their perimeter protection.
Security strategies are not something that can be changed overnight.
For these lagging organizations to truly be effective in providing
security, they must understand threats better and do everything to
get out in front, anticipate, and defend against their next move rather
than the previous one.
Instead of adding more cameras or investing
in traditional security solutions that
provide a limited threat response, the goal
should be to develop a new strategy and increase
awareness of activity beyond the view
of your fence or cameras.
Implementing an Approach
The major hurdle for organizations is implementing
an approach that focuses on realistic,
rather than hypothetical, threat behavior.
Real-world threats today operate in ways
designed to specifically counter most of the
modern, overt security technologies available
in the market.
To better understand the behavior and
activities of real-world threats, it’s imperative
to understand many of the misconceptions
associated with protection of many of our
protected facilities and assets.
Low level, insurgent-like behaviors, previously
confined to United States’ conflicts
in the Middle East, are now becoming more
and more prevalent in countries and regions
like the United States and Europe. Realworld
threats employ creative and unconventional
tactics that can only be understood
by studying their specific tactics, techniques,
and procedures. You cannot adequately protect
your assets against such threats by using
traditional red-teaming exercises and staff.
During recent conflicts in Iraq and Afghanistan,
we have seen conclusive evidence
that those seeking to do us harm will go to
great lengths to learn what and where existing
security measures have been put in place.
With that information, threats can understand
how to avoid and/or sabotage them
with little to no chance of recourse.
Even though these are concepts understood
by militaries and some security professionals,
most organizations are still planning
their protection around past attacks
even if it’s not representative of what could
happen today.
The 2013 sniper attack on the Metcalf
transmission substation is a constant reminder
of the type of attacks we are constantly
up against. With some early reconnaissance,
the attackers were able to quickly
cause $50 million in damages and escape apprehension.
Even with the amount of attention
this received in the security world, utility
providers and other organizations with highvalue
facilities have done little to improve
their protection.
Traditional perimeter security protection
tends to follow the same methodology no
matter what facility or asset you’re protecting.
A fence surrounds your protected area,
with cameras mounted at numerous positions.
These cameras are deployed to focus
on known routes and to reduce the amount
of surrounding blind spots. Security personnel
and sophisticated software monitor these cameras for movement and then react
when necessary.
The key is that they detect and react too
late. The detection and reaction sequence begins
at the point where the threat is already in
position to cause the most significant damage
or harm.
The result, most of the time, is that facility
security personnel end up watching
the camera feeds showing the damage as it
occurs rather than intervening early enough
in the process to prevent it from ever occurring
in the first place. To effectively secure
and protect physical assets from attack and/
or sabotage, you must incorporate standoff
capability into your protection plan. For
a security solution to be effective, you cannot,
knowingly or unknowingly, disregard
the threat activities and behaviors that occur
‘before the bad’.
In the majority of perimeter security applications,
cameras and other security solutions
are often mounted on or in the vicinity
of the ‘wall’ itself due to terrain and access
limitations. This is especially true in urban
areas with surrounding infrastructure or
places with blind spots caused by vegetation
and undulating terrain.
Unfortunately, this limited protection
that some facilities are constrained to adopt,
has now become universal throughout the
industry, no matter what the surrounding geography
looks like.
The Protection Plan
This type of protection plan, relying on fences
and cameras, also necessitates a certain
amount of staff available at all times who
can monitor cameras and respond to activity.
Security staff and expensive cameras are
two of the most common assets you have in
your facility’s protection architecture. Neither
of these options will prove to be cost effective
unless organizations learn to complement
them with low-cost solutions designed
specifically to make them more effective.
While this type of emphasis on “local”
protection along your physical perimeter and
last line of defense can create the perception
of comfort and security in your solution, the
reality is that it often creates a false sense of
security that ultimately translates into less
effective monitoring and response times by
security staff.
Lessons learned during recent insurgent
conflicts and counter-insurgency efforts have
only magnified these flaws and misconceptions
associated with the belief that bigger
fences and more cameras somehow equates to
more effective preventative security measures.
There’s a reason why we no longer fight
in castles surrounded by moats. It’s because
points of vulnerability not only exist along
your perimeter but also well beyond what
many today consider protected areas.
Regardless of your efforts to heighten
walls or construct barriers associated with
your physical perimeter, there will always
be vantage points or locations where you remain
vulnerable. A more effective and proactive
solution is one that allows you to monitor
well beyond that perimeter and makes
you aware of any threat-related activities
long before the threat ever reaches the point
where they are prepared to attack.
Advanced intrusion detection systems
are emerging alongside the industry’s pivot
towards more proactive security protection.
With a reduced false alarm rate and other advancements,
the issues associated with these
systems are becoming a thing of the past.
Organizational Solutions
Footstep detection, at extended ranges, is
a growing solution for many organizations
looking to get an advanced warning of threats
beyond their initial perimeter and protected
areas. Ground sensors, employed in conjunction
with traditional perimeter security approaches,
provide a cost-effective way to implement
a proactive strategy that ensures you
remain one step ahead of your threat.
Many of the ground sensor systems today
require cabling that inherently requires
trenches to be dug in order to conceal the
cables. The disturbed earth associated with
the buried footprint of such sensor systems
and associated cabling reveal a clear sign to
your threat of how and with what, you are
attempting to protect your assets.
Covert sensor systems exist today that
employs no cabling at all, that when buried
just below the surface of the ground, make
it nearly impossible for threats to conduct
surveillance on your facilities and assets.
Deployed asymmetrically, these sensors
not only transition your defensive posture
from reactive to proactive, but also easily
integrate with your existing security infrastructure
cameras, radars, and other technology
to make them more effective in their
employment.
Securing one’s facility and/or assets
against the ever-changing nature of threats
requires that the security industry collectively
begins to challenge the status quo and
look outside the box in order to be more proactive
in their efforts to reduce risk and prevent
the infliction of any
damage or harm.
This article originally appeared in the August 2017 issue of Security Today.