Hidden Backdoor in CCleaner Security App Has Infected 2.3 Million People
Hackers have hidden a backdoor in a security application called CCleaner. So far it has 2 billion downloads and has infected 2.3 million people and counting.
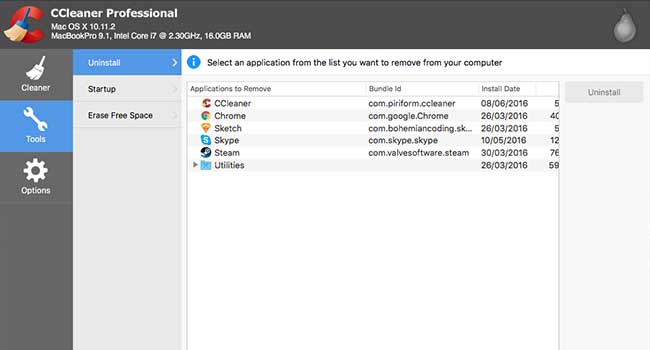
Security researchers have discovered cyber criminals have installed a backdoor in a security application for PCs. Users of the Avast-owned CCleaners for Windows have been advised to update their software immediately.
Researchers at Cisco Talos discovered the threat on Sept. 13 after CCleaner 5.33 caused their systems to flag malicious activity. The company warned that the hack could be comparable to the NotPetya ransomware outbreak, which spread after a Ukrainian accounting app was infected.
The hacked application allows for download of further malware, such as ransomware or keyloggers, and there are fears that virtually billions could be impacted. The security app has 2 billion downloads and claims to be getting five million extra a week, making the threat even more severe.
The backdoor installed in the application would send encrypted information about the infected computer - the name of the computer, installed software and running processes - back to the hacker's server. The hackers also used what is known as a domain generation algorithm (DGA) whenever the criminal's server went down, the DGA could create new domains to receive and send stolen data. Researchers have noted that the use of a DGA shows that these hackers are very sophisticated.
Further investigation found that the CCleaner download server was hosting the backdoored app as far back as Sept. 11 and the affected version had been released on August 15. Which means for weeks the malware was spreading inside a supposedly-legitimate security software.
On Sept. 12, CCleaner released an untained version of the software, version 5.34.