
Mobile Derived Credentials for Assured Identity for Federal Government
The solution is in hand, literally. It’s the mobile phone.
- By Dr. Sarbari Gupta
- Dec 27, 2017
Most U.S. Federal agencies rely on Personal Identity Verification (PIV) cards for staff authentication. The Department of Defense (DoD) uses the Common Access Card (CAC) for this purpose. The DoD has a bold vision for modernizing their authentication approach. However, the path from smart cards to next generation solutions has not been mapped. Furthermore, federal policy has not kept up with evolving technology.
The solution is in hand, literally. It’s the mobile phone.
Background
In June 2016, the DoD’s CIO Terry Havorsen made several speeches about potential changes to the department’s use of the DoD CAC which has been in use since 1999.
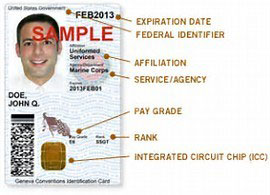 For experts in cyber security, replacing this card with an alternative system would be a challenge equivalent to U.S. President. Kennedy’s historic vision for space exploration. A huge base of people uses this technology for authentication on DoD networks and facilities. Without it, what's the alternative? Havorsen did not identify a specific alternative. Rather, Havorsen broadly indicated a desire for a multi-factor authentication solution that incorporates biometrics, personal contextual data or behavior-based techniques. The DoD realistically cannot phase out the more than 2.8 million CACs in use by the envisioned 2018 deadline. However, Havorsen’s ideas are timely as the CAC is not practical in constrained environments, such as theater of military operations. The CAC is also cumbersome to use with mobile devices, and does not enable secure interoperability with mission partners.
For experts in cyber security, replacing this card with an alternative system would be a challenge equivalent to U.S. President. Kennedy’s historic vision for space exploration. A huge base of people uses this technology for authentication on DoD networks and facilities. Without it, what's the alternative? Havorsen did not identify a specific alternative. Rather, Havorsen broadly indicated a desire for a multi-factor authentication solution that incorporates biometrics, personal contextual data or behavior-based techniques. The DoD realistically cannot phase out the more than 2.8 million CACs in use by the envisioned 2018 deadline. However, Havorsen’s ideas are timely as the CAC is not practical in constrained environments, such as theater of military operations. The CAC is also cumbersome to use with mobile devices, and does not enable secure interoperability with mission partners.
Also released in 2016 was an unclassified paper authored by Kim Rice, portfolio manager for DoD’s mobility program office in the Defense Information Systems Agency (DISA). In it, Rice focused the vision on DoD mobility. Rice’s position may be summarized as not about eliminating CAC as much as about enabling authentication from any location, using any device. Specifically, Rice called for enabling personnel to securely work in any location, on any device, and across any network.
Tehnology Solution
The proposed solution does not eliminate CAC, but instead builds upon CAC with a device that nearly all federal employees have – a mobile phone, in alignment with Rice’s approach to realizing Havorsen’s vision.
Currently, to obtain a CAC, much time and expense is invested in vetting individuals through an in-person registration and complex security background check process. The solution is to leverage that vetting by making the CAC the first-level credential for assured identity on a mobile device. If a person can prove CAC ownership, one can authenticate using a pin or biometric, as well as a second method of authentication that only the true card owner can confirm.
Modern devices have embedded universal integrated circuit cards, commonly known as SIM cards which allow for stored, encrypted data. Mobile phone companies have their own incentives (billing based on usage) to offer these features. Mobile authentication would leverage the technical capabilities built into in these commercial products. Depending on the level of assurance needed, there could be a non-embedded or embedded crypto token implemented via hardware or software.
Admittedly, there are inherent security challenges with mobile devices, such as:
-
Small devices are easy to lose
-
Passwords may not be enabled out of user convenience
-
Multiple channels of attack are possible -- unsecured Wi-Fi, malware, unauthorized jailbreak, out-of-date security updates, obvious passwords, malicious websites, etc.
However, there are several ways to mitigate these challenges, like recommendations in the U.S. Government Accountability Office’s Report to Congressional Committees on Information Security, “Better Implementation of Controls for Mobile Devices Should Be Encouraged.”
End Users
End users can mitigate these threats to better secure their mobile devices by:
-
Maintaining physical control of the device
-
Enabling user authentication
-
Limiting the use of insecure communication channels. For example, if one is connected to a Wi-Fi at a coffee shop and sends critical communications, then a person sitting nearby could track all the activity, essentially eavesdropping.
-
Downloading apps only from reputable sources
-
Installing security software
-
Promptly installing security updates
-
Enabling the remote wipe of data
Agencies
On mobile devices issued by the government, there will be an MDM solution that ensures every device has the latest security patch and two-factor authentication, in addition to more controls. The MDM is always watching. Some things are impossible to undo, but others may be comprised if the user plays with the settings. The MDM ensures the mobile device is still configured securely.
Agencies can mitigate threats to better secure their employees’ mobile devices by:
-
Establishing and implementing a mobile device security program, including user training that frequently emphasizes user impact. The agency can implement strong technical controls, but if the user is cavalier, there will be vulnerabilities.
-
Implementing layered security, such as authentication to device, cryptographic protection of data and transactions, and user training and awareness of security risks.
-
Creating a mobile device management (MDM) solution that runs in the background and partitions a “sandbox” environment, as well as managing the security configuration on the device, implementing two-factor techniques, and encrypting stored data.
Policy Challenge
In addition, to a new technology solution, the government’s personal identification verification (PIV) credentials standards need an update. Specifically, NIST Special Publication 800-157 on Guidelines for Derived PIV Credentials (nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-157.pdf) does not allow the use of mobile derived credentials for authentication to a second platform in lieu of a PIV card. Therefore, one cannot, in terms of regulatory policy, use the derived credential on a mobile device to logon to a laptop or desktop. In other words, the current government standards do not allow for mobile derived credentials for assured identity. This needs to be updated.
Conclusion
The DoD was initially thinking that in a technical environment it would not need to use the CAC card. But if the CAC is eliminated, another authentication solution is required. However, the biggest expense associated with the CAC is not the plastic card itself; it is the background checks and paperwork that have been done to vet the individual to whom the card was issued.
The solution is leveraging derived credentials on mobile devices as one important component of an assured identity solution that does not involve CACs. The technology infrastructure is available, but the standards must be updated in accordance with the need, vision, and technological capabilities.