
Equifax says the two breaches are unrelated.
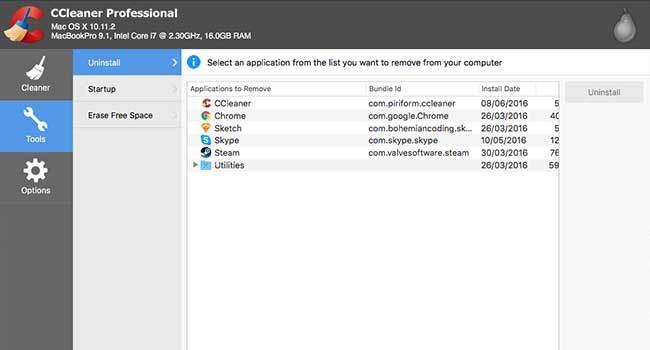
Hackers have hidden a backdoor in a security application called CCleaner. So far it has 2 billion downloads and has infected 2.3 million people and counting.

Breakthroughs in technology mean that connected cars are shunning physical keys in favor of digital, smartphone-based entry systems.

The US government has officially banned the use of Kaspersky security software in all of its federal agencies.
A set of vulnerabilities present in "almost every" device with Bluetooth capabilities has been revealed by researchers at security firm Armis.

The iOS 11 has been in beta testing for a few weeks now and many users are reporting a new discovered security feature that could boost a user's data security and make it harder for police to find information.

A recent incident in upstate New York has shown that even police departments aren't immune from hacking.

The Atlanta-based company announced the hack on Thursday, and said that intruders were able to access customers' Social Security numbers, addresses, names, birthdays, driver’s license numbers and more.
- By Nicole Crites
- Sep 08, 2017

Gaping security holes have been discovered in most AT&T U-verse cable modems that would allow remote cyber criminals to access a household’s internet connection as well as any devices connected to it.

Moving to higher ground within the commercial enterprise space.
- By Gerald Hubbard
- Sep 05, 2017

The Facebook-owned social media company sent an email to high-profile users on Wednesday alerting them that a bug in its software may have allowed users’ account data to be accessed.

Law enforcement and security professionals can benefit from the IoT — and not just to watch people more closely. Follow these three steps to prepare for the IoT reality, protect your own vulnerabilities, and find creative solutions to your investigative problems.
- By Danny Boice
- Sep 04, 2017

While our industry is fairly good at anticipating and reacting to new physical security threats, we’ve been very slow to react to the clear and present danger from cybersecurity attacks.
- By Tom Galvin
- Sep 01, 2017

The FDA issued a security advisory, warning that the pacemakers must be recalled on a voluntary basis. The devices are much “smarter” than previous models, opening up the possibilities of being tampered with by cyber criminals.

DJI is not happy with companies denying their products based on security fears.

When it comes to mobile security, pairing biometrics with device authentication is a logical defense against attacks.
- By Michael Lynch
- Aug 28, 2017

In an effort to better compete against Amazon and Microsoft in the cloud computing space, Google will reveal the technical details of its new security feature, the Titan computer chip.
Nearly 50 vulnerabilities have been found in industrial collaborative robots which can be configured enable the robots to spy on their surroundings or cause physical harm to workers

For the second time in a month, HBO has fallen victim to cyber criminals.
The U.S. Army banned the drones after they detected “cyber vulnerabilities.”