Common sense dictates that it is easier to stop something from happening in the first place than to repair the damage after it has been done.
- By Siva G. Narendra
- Jul 01, 2017
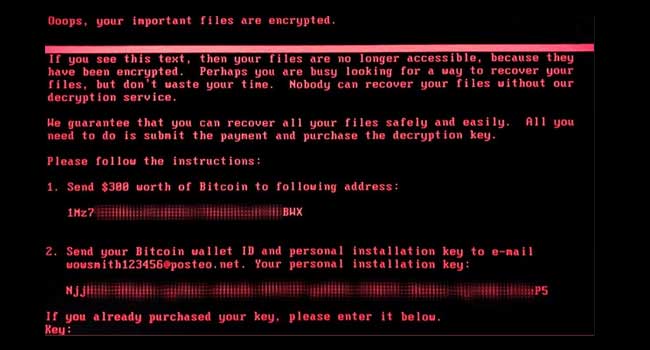
Yesterday, PC users across the world were asking for help as ransomware took data hostage and locked users out of their computers.

Government websites in Ohio, Maryland and New York were targeted.
Fewer than 90 email accounts with weak passwords are believed to have been hacked in “sustained” attack.

The education program is being developed in a partnership between the Girl Scouts and Palo Alto Networks.

For a relatively long time it seemed as if the password problem had been solved using SMS text messages.
- By Michael Lynch
- Jun 22, 2017

The cybersecurity arm of British intelligence services has reportedly suggested the global ransomware attack was launched from North Korea.

MacSpy is being advertised as the “most sophisticated Mac spyware ever.”

While many security teams at retailers are concerned about the potential for a big data breach, everyday security threats, like social engineering and shoplifting, are heightened in a world of omni-channel retail.
- By John Carter
- Jun 01, 2017
The risk posed by hackers to the Internet of Things (IoT) is a hot topic and there have already been some serious real-world attacks.
- By Christopher Camejo
- Jun 01, 2017
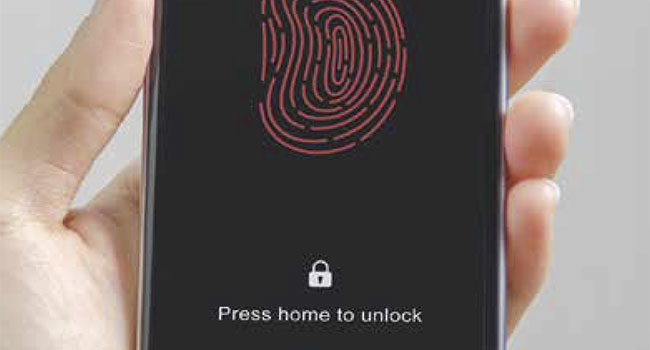
When used effectively, biometrics can contribute to safer cybersecurity practices.
- By Alisdair Faulkner
- Jun 01, 2017

Chipotle has released a nationwide list of stores that were targeted in the security breach between March and April of 2017.

Companies are asking China to delay the implementation of a new cybersecurity law amid concerns of how the legislation will affect personal information and cloud computing.

The WannaCry attack started last Friday and has affected 200,000 computers in almost 150 countries around the world.
- By Peter Butler
- May 18, 2017

What's next for agencies under the new executive order?
- By Mike Shultz
- May 16, 2017

Cybersecurity experts expect there will be more people falling victim to the worldwide cyberattack that hit on Friday.

Several British Hospitals say they are experiencing major computer problems as the result of a breach in cybersecurity.

President Trump has signed an executive order to strengthen the government’s cybersecurity.

Just days ahead of the French Presidential Election, candidate and now France’s president-elect announced his campaign had been hacked.

It’s time to take the pledge to improve your password habits.