According to a number of studies, hospital crime and violence have been growing at an alarming rate in recent years. The wide variety of security threats that healthcare facilities face include theft by employees or visitors, violence or threats from visitors or patients, and other crimes of opportunity.
- By Jennifer Hackenburg
- Oct 01, 2017
Throughout the course of a calendar year, we take a look at numerous security solutions, events and, in our case, publications. In this issue, we have a specialty publication that focuses on government security. Security in the public sector is a big deal.
- By Ralph C. Jensen
- Oct 01, 2017

When a regional traffic management center in Washington state outgrew its building—as well as the size of its roadway monitoring system— the staff realized it was time not just for a physical upgrade, but a technological one, too
- By Kevin Christopherson
- Oct 01, 2017

Where is all the money in the marijuana business going? Who is moving the cash or product as it seems to be in the news all the time? Here we share why it’s important to your business that you know how this is all happening.
- By Todd Kleperis
- Oct 01, 2017
If there is any question about Dallas as a host city for ASIS, that should be cleared up after day one of 2017 ASIS. My opinion and observation is that attendees crowded the aisles and show floor in number this exhibition hasn't seen in years.
- By Ralph C. Jensen
- Sep 27, 2017
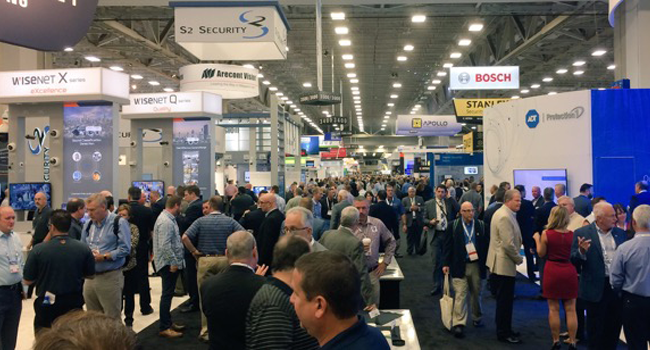
If there is any question about Dallas as a host city for ASIS, that should be cleared up after day one of 2017 ASIS. My opinion and observation is that attendees crowded the aisles and show floor in number this exhibition hasn't seen in years.
- By Sydny Shepard
- Sep 27, 2017
ASIS attendees staying at the downtown Dallas Hampton Inn got a rude wake-up call at about 3 a.m. this morning as a fire in a nearby parking structure forced an evacuation of the hotel.

The Importance of Locking Down Multiple Devices in the Office
Anixter has a Blue Book that serves as a corporate bible; Pat Comunale, president of Anixter’s global security solutions, believes in the book from the first page on, and it would seem the Blue Book is, as he notes, second to none.
- By Ralph C. Jensen
- Sep 01, 2017
As a security professional, how many times have you had to explain why a PTZ camera should always be paired with at least one fixed camera to provide constant “back-up” coverage of everywhere the PTZ is not looking?
- By Bret McGowan
- Sep 01, 2017
I have a great job. I’ve met many wonderful people in the past 20 or so years, and when we started Dealer Strategies, it gave me the opportunity to go one on one with company CEOs and some of their staff.
- By Ralph C. Jensen
- Sep 01, 2017
As a security integrator, you’re used to having a predictable revenue model selling security hardware and software to end users.
- By Greg Schreiber
- Sep 01, 2017
Why the recent increase in turnstile demand? Some of the reasons are the aging post-9/11 turnstile systems (15+ years), concerns over violence and terrorism, and tenants’ expectation of secure entrances in property management buildings.
- By Mike McGovern
- Sep 01, 2017

Putting together the proper leadership team may be an overwhelming task. It has to be created carefully and properly, and it has to work to be successful.
- By Ralph C. Jensen
- Sep 01, 2017

Richard Rawlings is the kind of guy that keeps track of everything in his shop, and when his Gas Monkey Garage started booming, an up-to-date security system was critical.
- By Ralph C. Jensen
- Sep 01, 2017

The Ottawa Elementary School District is in Ottawa, Illinois, a river town 80 miles southwest of Chicago. In the spring of 2015, a variety of issues caused the schools’ administration to determine that they needed a surveillance system upgrade.
- By Jeff Whitney
- Sep 01, 2017

The DIY systems that are emerging today are the next logical step for the growth of the security industry. The key to their success will be making these systems easier to install and easier to use.
- By Steve Connor
- Sep 01, 2017
Effort means a lot, of course, since it’s hard to find anyone who turned a profit by being lazy. But for security companies, especially smaller integrators who are trying to compete with gigantic competitors, it’s not enough just to work harder than the other guys.
- By Robert Ogle
- Sep 01, 2017
When it comes to choosing cabling infrastructure for security, it is essential to work with a distribution partner that can provide the right education, training and products for your project needs.

The security industry has seen rapid growth in the use of apps to enable security solutions. For every customer need, there is a budding idea for a mobile solution.
- By Brad McMullen
- Sep 01, 2017