
Dixon High School's School Resource Officer has been called a hero after interrupting a student who fired several shots in the school.
- By Sydny Shepard
- May 18, 2018

One person has died and three others were injured in an explosion that happened at a medical facility in Southern California on Tuesday afternoon.
- By Sydny Shepard
- May 17, 2018

Local police said they began preparing security plans for the big day as soon as the couple disclosed details on the venue for the wedding.
- By Sydny Shepard
- May 15, 2018

Using a robust, web-based ID software to create credentials with high-security features for a community’s public employees

Florida hospitals install new security protocols aimed at visitor management.
- By Sydny Shepard
- May 09, 2018

The Philadelphia Phillies are improving security around Citizen Bank Park with perimeter protection devices.
- By Sydny Shepard
- May 09, 2018
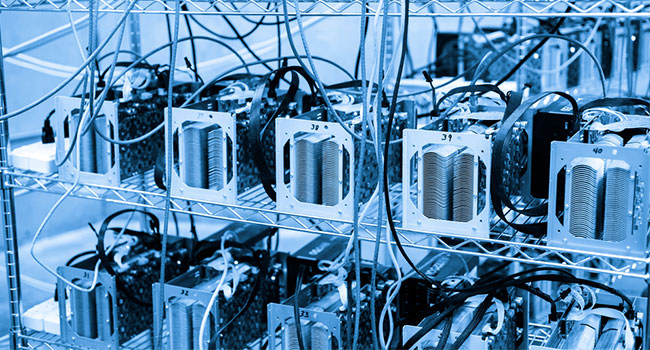
Utility companies in Washington State are boosting security after placing a moratorium on cryptocurrency miners.
- By Sydny Shepard
- May 08, 2018

A civilian loss prevention officer and two Dallas police officers were shot at a Home Depot in the Texas city.
- By Sydny Shepard
- Apr 25, 2018

A new survey found that 48 percent of U.K. factories have been hit by a cyberattack.
- By Sydny Shepard
- Apr 24, 2018

Police continue to search for a 29-year-old suspect that killed four people and injured three more at a Waffle House near Nashville.
- By Sydny Shepard
- Apr 23, 2018

The citywide effort, dubbed Safe Smart CLE Initiative, will enable police to brighten lights in trouble spots and monitor camera-covered areas in real time.
- By Sydny Shepard
- Apr 23, 2018

A new survey found that 38 percent of hackers believe they can access any healthcare data they want to in under an hour.
- By Sydny Shepard
- Apr 19, 2018

Several companies at ISC West are dedicated to bringing safety and security to campuses across the country.
- By Sydny Shepard
- Apr 18, 2018

Several hours of fighting at a maximum security prison in South Carolina led to the death of seven inmates.
- By Sydny Shepard
- Apr 17, 2018

Three people were shot at the YouTube HQ in San Bruno, Calif.
- By Sydny Shepard
- Apr 04, 2018
Technology marches ever forward, lockstep with ‘Moore’s Law.’ However, the influx of technological change affects different industries in different ways.
- By Andy Newbom
- Apr 01, 2018

The Fire Service was effectively "outside the loop."

Cybersecurity was found to be the top technology used by healthcare facilities.
- By Sydny Shepard
- Mar 06, 2018

The safety and security of visitors and staff and the protection of the Musical Instrument Museum's extensive collection is an essential aspect of fulfilling its mission. With an active facility during both day and evening hours, the museum sought to upgrade its outdoor security surveillance system to improve the quality of the images around the clock.
- By Sydny Shepard
- Mar 01, 2018

Perimeter protection has been part of the human psyche since the dawn of mankind. Over the millennia we’ve evolved from crude barriers of sticks and rocks to fortified walls of concrete and stone to electrified fences and high-resolution surveillance cameras.
- By Joe Morgan
- Mar 01, 2018