Securitas is acquiring Supreme Security Systems, a top 50 alarm monitoring company in the United States.

Security technology manufacturer, Paxton, has updated their popular Paxton Connect app to make remote site management simpler than ever before.

Genetec Inc. has announced the industry’s first enclosure management solution that gives traffic managers and engineers the ability to remotely manage, monitor, and secure traffic enclosures.

According to national news sources, the Michigan teenager accused of killing four students and injuring six others at Oxford High School in Oxford Township, Mich., on Tuesday will be charged as an adult. Ethan Crumbley, 15, faces two dozen charges including murder, attempted murder and terrorism.
- By Matt Jones
- Dec 03, 2021

Investing in information security has never been more critical. The COVID-19 pandemic has reshaped the way we work, stressing our systems, connections, and networks. Cyberattacks continue to make headlines, and physical data breaches remain a concern.
- By Michael Borromeo
- Dec 03, 2021

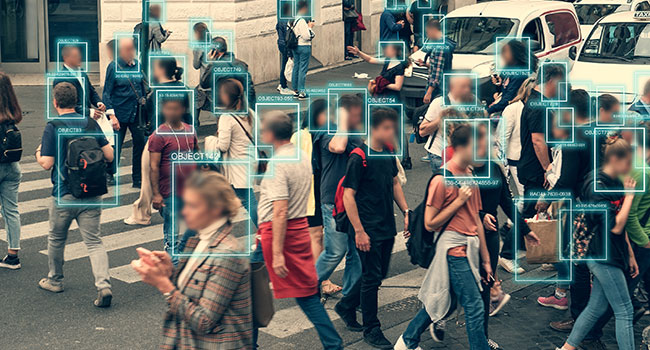
City populations are growing and our resources are under strain. That’s why we need to rethink city living – not tomorrow but now. Fortunately, many forward-thinking city authorities are showing us a way to address this, based on connected video technology.
Carrier Global Corp. is pleased to announce its participation in the International Society of Automation Global Cybersecurity Alliance (ISAGCA).

The global pandemic accelerated a worldwide digital transformation that has simultaneously reduced or eliminated physical touchpoints and in-person contact.
- By Stephen Carney
- Dec 01, 2021

Over the last year and a half, the retail industry has undergone massive changes. Retailers of all sizes have shown extraordinary resilience and creativity by reshaping their business models and operations.
- By Sean Foley
- Dec 01, 2021

What once began as technology typically reserved and embraced by law enforcement, wearable video continues to find applications and use-cases in a host of new verticals and industries.
- By Jason Ouellette
- Dec 01, 2021

We have all read or heard about incidents of cybercrime targeting government and commercial entities to compromise services or harvest information. As you can image, financial institutions are a primary target for attack.
- By David Uberig
- Dec 01, 2021
During the week of Halloween, American Airlines and Delta Air Lines were the latest to have to deal with “domestic terrorism” at 38,000 feet. Where does this behavior come from?
- By Ralph C. Jensen
- Dec 01, 2021
Let’s admit it. When analytics first hit the market, they got off to a rocky start. Lots of hype, and high expectations. When it came to delivering on those promises, their performance often fell short of the mark.
- By Robert Muehlbauer
- Dec 01, 2021
Throughout time, securing the data in our communications with others has always been a major concern. Perhaps the prehistoric men or woman, were the only civilization in history that didn’t have to worry about someone getting their hands on someone else’s messages.
- By Richard Kanadjian
- Dec 01, 2021
The pandemic has impacted enterprises across nearly every single market sector. Sudden shutdowns, supply chain disruptions, labor shortages and an uptick in violent crime have each wreaked havoc on businesses large and small in the United States, and all over the globe.
- By Jason Burrow
- Dec 01, 2021
To ease cost pressures, facility operators must find ways to improve a variety of elements within their buildings, including their security system.
- By Dave Karsch
- Dec 01, 2021

Whether it is water, electricity, gas, oil or even telecommunications and transportation hubs, critical infrastructure facilities present unique challenges for security professionals.
- By Michael Shipley
- Dec 01, 2021
Security is a consideration in the evaluation of all technology today. We want to make sure that every device is physically secure, that control of the device is secured, and that the data going to and from the device is also secure.
- By Brian Pickowitz
- Nov 29, 2021