
Chinese manufacturer DJI, which accounts for about 70 percent of the global drone market, stands to lose the most from a ban, which is based on national security concerns.
- By Haley Samsel
- Mar 13, 2020

The original show was postponed in March due to concerns over the coronavirus (COVID-19) crisis that has spread globally.
- By Haley Samsel
- Mar 13, 2020
Lars Thinggaard will leave the company in April and promote his new book

After airport security screeners called for the government to provide N95 respirators instead of surgical masks, the CDC has begun to make them “optional” for those employees.
- By Haley Samsel
- Mar 11, 2020

Americans need to be on the lookout for malicious domains created by scammers as well as widespread disinformation and conspiracy theories being spread online.
- By Haley Samsel
- Mar 10, 2020
Meekins, who previously worked at Open Options, Salient Systems and more, will be responsible for growing sales in the east

Despite concerns about Chinese manufacturers having access to U.S. transportation data, cities continue to move ahead with plans to partner with state-owned companies.
- By Haley Samsel
- Mar 09, 2020

Show organizers are planning to hold one of the security industry’s largest conferences in July after several companies indicated they would not send employees to the show.
- By Haley Samsel
- Mar 06, 2020
Technology executive and business transformation specialist joins majority-female C-suite

There was no significant increase in disinformation campaigns or hacking attempts like there were in 2016, according to top Homeland Security officials.
- By Haley Samsel
- Mar 05, 2020

The pharmacy would not say how many people had been affected by the error, but said that prescription data and customers’ names were part of the leaked information.
- By Haley Samsel
- Mar 04, 2020
Advanced will become a division of USA Security, both of which are based in New Jersey
Jackson joins the company after serving as regional vice president of RightCrowd Software
ISC West, the largest converged security event in the U.S., today introduces the lineup for its 2020 SIA Education@ISC sessions, in collaboration with premier partner the Security Industry Association (SIA).
Boon Edam recently announced they are unveiling a new optical turnstile addition to their security entrance portfolio at the ISC West Exhibition in Las Vegas, March 18-20, 2020 in booth #8037. This will be the first opportunity for show attendees to see the Speedlane Compact, which is scheduled to be available in the fall of 2020.

Clearview is also piloting a video surveillance camera with live facial recognition capabilities and has tried to expand into other countries in the Middle East and Asia.
- By Haley Samsel
- Mar 02, 2020
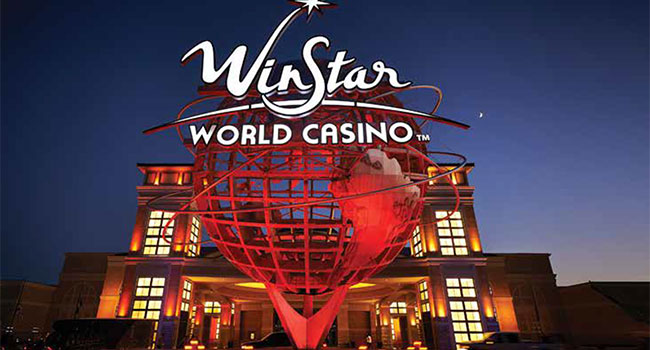
The Chickasaw Nation is a federally recognized, independent Native American nation located in south-central Oklahoma. The nation’s territory covers more than 7,600 square miles and is home to a population of nearly 70,000.
- By Ralph C. Jensen
- Mar 01, 2020
ERDC enlisted the services of M3 Technology Group, an audio-visual integrator based in Nashville, Tennessee, to create a unique audio-visual experience not seen in other government facilities.
- By Michael Callahan
- Mar 01, 2020