
The Fire Service was effectively "outside the loop."

Users are downloading their Facebook data to see just how much Facebook is recording.
- By Sydny Shepard
- Mar 27, 2018

Market Research Future found that Industrial Access Control is expected to reach $1.03 billion by 2023.
- By Sydny Shepard
- Mar 27, 2018

The cyber theft campaign was targeting American universities, companies and government entities.
- By Sydny Shepard
- Mar 26, 2018

The video promotes the organization's anonymous reporting system.
- By Sydny Shepard
- Mar 26, 2018

High-ranking security executives at Google, Facebook and Twitter—three of the Internet’s most important technology companies—have announced this week plans to leave their respective positions.
- By Jessica Davis
- Mar 23, 2018

Highway Patrol troopers will join the security team at Majory Stoneman Douglas High School.
- By Sydny Shepard
- Mar 22, 2018

The teenager ultimately decided to share his findings because he was afraid it would not be explained correctly to customers.
- By Sydny Shepard
- Mar 22, 2018
Alan has more than 10 years of commercial security experience.

The suspect in the Austin bombings detonated a bomb in his car as officers closed in.
- By Sydny Shepard
- Mar 21, 2018

UT Austin, Austin Country Club and the neighborhoods in the area are boosting security following the serial bombings.
- By Sydny Shepard
- Mar 21, 2018
Brent awarded for leading collaborative efforts and leading SIA International Relations Committee.
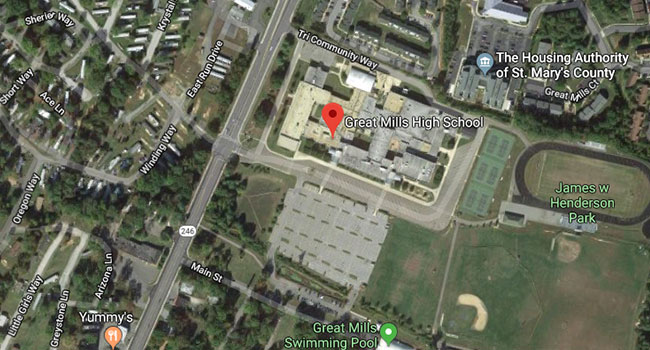
Police in southern Maryland are responding to a call at Great Mills High School were several people have been injured in a shooting.
- By Sydny Shepard
- Mar 20, 2018

According to cybersecurity firm Kromtech, who found it stored in a publicly accessible Amazon S3 bucket.
- By Sydny Shepard
- Mar 20, 2018

Package bombs left on porches in Texas have killed two people and wounded two more.
- By Sydny Shepard
- Mar 19, 2018

Connected devices at home can record the voices, movements, weight and eating habits of those who live there. They are, in effect, very sophisticated sensors installed in the home environment. As such, they can be utilized by all sorts of people with various motivations and intentions of harming us.
- By Yotam Gutman
- Mar 19, 2018

A gunshot-detection system hailed by the Pittsburgh police is poised to cover nearly a third of the city this year.
- By Sydny Shepard
- Mar 19, 2018