Police Virus Infections on the Rise Reported PandaLabs
PandaLabs, the anti-malware laboratory of Panda Security, released new data around the rise of the 'Police Virus'. Despite the arrest of the cyber-criminals allegedly responsible for the 'Police Virus' ransomware attacks, this infamous piece of malware has continued to infect thousands of computers around the world, according to data gathered from December 2012 to February 2013 by PandaLabs.
The vast majority of these infections are caused by "exploit kits," applications that allow attackers to infect users' computers simply by getting them to visit a compromised Web page. Cyber-criminals take advantage of security flaws in popular programs - such as Adobe Acrobat or Java, for example – to gain control of systems. At present, there are still a lot of variants of the Police Virus in circulation, all of them detected by PandaLabs as Trj/Ransom.AB.
In an international operation, led by the Technological Investigation Brigade of Spain's National Police force and coordinated by Europol and Interpol, the arrest of the cyber-gang leader in Dubai has not put an end to the malware epidemic.
"This ransomware was netting profits in excess of $1.3 million per year," explained Luis Corrons, technical director of PandaLabs. "However, the number of infections keeps growing, which leads us to think that we are facing an unspecified number of groups launching the same kind of attacks."
'Police Virus' is still active
This malware epidemic has continued to infect hundreds of thousands of computers around the world, using fear and blackmailing techniques to extort money from computer users. The scam is very lucrative and has evolved over time, using various techniques to trick users. The most recent evolution even shows images taken with the users' webcams, making the scam all the more realistic.
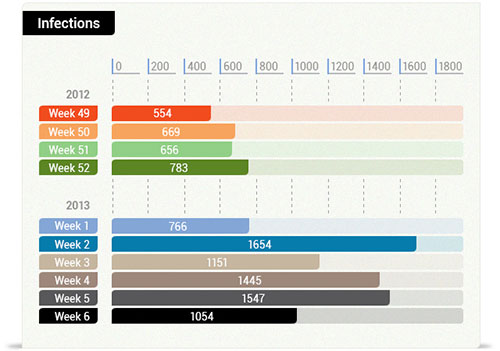
In fact, research carried out by PandaLabs, on two of the malware families used in the attacks, has revealed that the number of infections has doubled from 2,500 to more than 5,000 since the arrest of the ringleader in December 2012.
PandaLabs offers users a couple of tips to avoid falling victim to this type of scam:
- Keep your computer's software (including the operating system and all installed programs) up-to-date; and
- Disable Java in your Web browser, or uninstall it completely if you don't need it.
Panda Security, The Cloud Security Company, has launched a new version of its free antivirus software, Panda Cloud Antivirus, neutralizing malware that takes advantage of any of the vulnerabilities exploited by the Police Virus.