Real Time Technology Group Named 2013 Computerworld Honors Laureate
 Real-Time Technology Group (RTTG), a provider of trusted identity solutions, has been named a 2013 Computerworld Honors Laureate. Founded in 1988, the honors program recognizes organizations and individuals who have used information technology to promote and advance public welfare, benefit society and business, and change the world for the better.
Real-Time Technology Group (RTTG), a provider of trusted identity solutions, has been named a 2013 Computerworld Honors Laureate. Founded in 1988, the honors program recognizes organizations and individuals who have used information technology to promote and advance public welfare, benefit society and business, and change the world for the better.
To select this year's Laureates, Computerworld relied on a panel of 22 distinguished judges -- many of them Computerworld Premier 100 IT Leader Honorees from diverse industries -- to evaluate the humanitarian benefits and measurable results of applying technology to meet a specific social or business need.
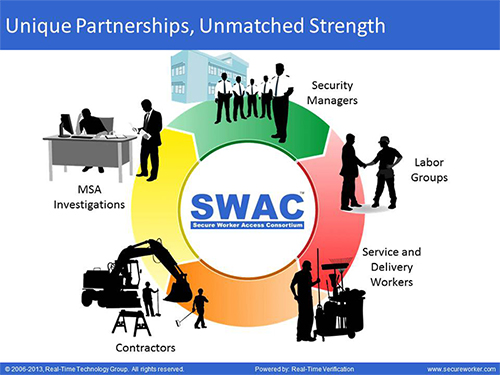
Real-Time Technology Group, and its Secure Worker Access Consortium (SWAC) project, was selected from more than 700 nominations to become one of 268 Laureates from 29 countries. SWAC is a single project that unites the efforts of 2800+ labor groups, private contractors, public agencies and security professionals to deliver a shared solution for enhanced access control. Enabled by RTTG’s Real-Time Verification (RTV) technology, SWAC brings together public agencies and private enterprises to cooperatively secure critical infrastructure through personal identity verification, criminal background screening and authentication of workers’ credentials for secure access to sensitive facilities, like the World Trade Center construction project.
SWAC securely collects and privately manages members' personal information; verifies workers' identities and threat-free backgrounds; provides real-time information for authentication of access rights at critical infrastructure sites; audits the history of every member's activities; supports a trusted contractor community that is known, skilled, threat-free, and stands ready to serve our nations' sensitive sites; and ensures maximum personal privacy protection.
Using secure, Web-based hosting, SWAC enables credentialing information to be securely transferred in real time to any entity anywhere in the world with only a Web connection. SWAC was first implemented in 2007 and adopted by the Port Authority of New York and New Jersey. It was contractually renewed again in 2012 and has expanded over the years to include other major metro, New York-area agencies including Metropolitan Transit Authority, New Jersey Transit, New Jersey Turnpike Authority, New York Thruway Authority, New York Bridges Authority as well as the Army Corp of Engineers.
Computerworld will host its black tie Awards Ceremony and Dinner in Washington, D.C. in June. Daniel Krantz, Real-Time Technology Group CEO, will be recognized and presented with a medallion inscribed with the program's mission, "A Search for New Heroes."
"I am extremely humbled and honored that Real-Time Technology Group has been named a Computerworld Laureate," Krantz said. "A leading source for technology news and information, their prestigious honors program recognizes people and organizations that use information technology to promote positive social, economic and educational change. To have earned that distinction from Computerworld means a great deal to me and my RTTG partners who have worked since 1999 to develop our capabilities."
“Technology continues to play a pivotal role in transforming how business and society functions," added John Amato, vice president and publisher, Computerworld. "For the past 25 years, the Computerworld Honors Program has had the privilege of celebrating innovative IT achievements. Computerworld is honored to recognize the outstanding accomplishments of the 2013 class of Laureates and to share their work. These projects demonstrate how IT can advance organizations' ability to compete, innovate, communicate and prosper.”