
What Does the Near Future Hold for ID Cards and Credentials
- By Jeremy Earles
- Jul 16, 2013
Every security professional, integrator and user needs to be aware of the three major initiatives for cards and credentials: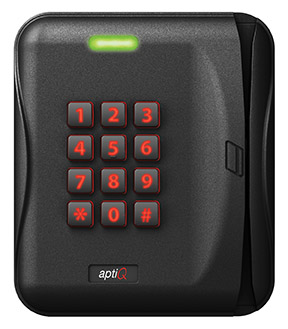
- Smart cards are becoming the credential of choice. Now is the time to start planning for the switch from magnetic stripe and proximity cards to smart cards.
- It’s going to be a hybrid world. Although smart cards may be the credential of choice, multiple types of credentials such as key systems, PINs, various types of cards and biometrics will still be necessary for certain operations. Adding special credentials to such areas is possible; and, if using multiple credentials, one system to manage them all will probably be important.
- Get ready for new technologies, such as NFC (near field communications). With NFC-enabled smart phones, employees and customers can use their own smart phones as access credentials, just like using smart cards.
The Technology behind Smart Cards
While 125 kHz proximity technology and magnetic stripe cards are the common technology in today’s access systems, 13.56 MHz smart card technology is the technology of tomorrow. Bottom line – it provides more security and storage for access control systems, not to mention the cost of a smart card is comparable to that of the standard, traditional proximity card.
Not only does a smart card provide much higher security than a proximity card, it handles a wide variety of applications from holding biometric templates to being used for cashless vending. It is very important that all facilities be prepared for smart credential deployment, even if that facility only wants to install proximity technology at present.
A Single Smart Credential
Besides making access control more convenient, smart cards can be used for time and attendance, logical access, cashless vending, cafeteria payments, and checking out scrubs and medical equipment, just to name a few. All of those functions can be consolidated onto a smart card, creating an efficient environment where staff would have only one credential to use throughout their day.
Administrative costs and productivity. Not only is the cost of a single credential lower than purchasing multiple forms of ID, but the reduced management and distribution time for one credential will have a significant impact on productivity.
Increased security. Smart credentials increase the security of the information kept on the card and stored in the facility. In comparison to door keys, magnetic stripe cards or proximity cards, the encrypted security of smart credentials ensure that they are more difficult to counterfeit.
IT-approved. When presenting a smart card solution, be prepared for representatives from the IT department to take notice, as more and more security system decisions are being made with input from the IT department. Because of this, there is an increased desire for the convergence of physical and logical security access control.
IT professionals want strong authentication credentials, the level of security provided by smart cards. Contrary to proximity cards, magnetic stripe cards and their readers, smart cards go through a challenge and response sequence to initiate conversations with the network, and these communications are encrypted using industry-standard, encryption techniques.
By welcoming the involvement of the IT department, and showing the ability to speak their language and answer their questions, you will gain additional layers of approval within the organization.
Multi-credential readers. Besides aiding implementation, multi-technology readers are available to create flexibility during the transition while allowing you to leverage the benefits of smart cards now or in the near future.
Installing a multi-credential reader at every new door means you are able to flexibly plan for the future. Since multi-technology readers work on both the proximity and smart card frequency, they can still use current proximity credentials, while migrating to smart credentials at their own pace. Likewise, multi-technology readers can read both magnetic stripe and smart cards.
The transition. You can use your old credential and new smart credential, while upgrading on your preferred timeline, not on the whim of technology that forces a "now-or-never" alternative. And, when you switch to smart cards, you will not have to tear out and re-install all of your facilities’ readers, because the multi-card readers are ready to go.
Applications other than access control. Be sure to choose the right smart card credential by looking for platforms that are open format rather than those designed for proprietary systems. Open formats allow easy integration into other applications with minimal programming while speeding up the time of deployment, reducing the cost of implementation and giving more freedom to get the most out of your investment.
Our Smartphone as our Credential
Over 285 million NFC-enabled smart phones are expected to be sold in 2013, and over half the phones sold in 2015 will be NFC-capable.
Existing aptiQ 13.56 MHz smart cards/multi-technology readers are already compatible with the new NFC technology, allowing users to deploy their own smartphones as their credentials to enable secure access into their facilities. When NFC-enabled phones are available, it won’t be necessary to replace your present smartcard/multi-technology readers. When transitioning and planning for future expansion, spanning the various technologies of the past, present and future with a multi-technology reader only makes sense.
Other Credentials
For higher-security applications that require multiple forms of verification, the smart card has an advantage, because it securely stores other credential types such as biometric templates, PIN codes and photos right onto the smart card. This provides an extra level of security at the access point, protecting the information behind closed doors or on the secure network, without added inconvenience to the user. For instance, more and more data rooms, laboratories and other “high asset value” rooms are being protected with biometrics to ensure that the person attempting to enter is the person who is authorized to have access. Of course, not all access points – such as the broom closet – are high security locales, so for these doors, keys may remain in service for some time.
With multiple types of credentials, it is imperative that an open architecture is selected for more flexibility and scalability, and a growth path. Remember, security applications are frequently installed in stages. Too often, over the years, different brands with various operating mechanisms can get installed, and the products operate independently, without integration into one system. This is usually due to the hardware and software systems being proprietary and not compatible with other components.
Security directors today need to choose access control systems that can be upgraded to create an enterprise security system: a system that can meet current safety and security issues, as well as accommodate emerging technologies that allow the system to expand and adapt as needed. Such solutions should be able to operate current technologies, as well as those under development, without compromising or risking investments in present systems.