
Trapping Terahertz Rays for Better Security Scanners
Medical diagnostic and security scanners with higher sensitivity could result from University of Adelaide research into detecting T-rays (terahertz waves).
Published in the journal Advanced Optical Materials, the researchers describe a novel structure that traps terahertz waves in tiny (micro-scale) holes to produce much higher contrast imaging than currently possible.
 Terahertz waves, which are electromagnetic waves with frequencies between those used for mobile phone communications and for optical fiber communications, are used for some airport body scanners and other security scanners to see through packages and clothes. They are also capable of distinguishing malignant from healthy tissues for Cancer detection.
Terahertz waves, which are electromagnetic waves with frequencies between those used for mobile phone communications and for optical fiber communications, are used for some airport body scanners and other security scanners to see through packages and clothes. They are also capable of distinguishing malignant from healthy tissues for Cancer detection.
“This work takes an unconventional path to detecting terahertz waves,” said Dr. Withayachumnankul, project leader and ARC Postdoctoral Fellow in the University’s School of Electrical and Electronic Engineering.
Dr. Withayachumnankul has worked with RMIT University in Melbourne and Albert Ludwigs University of Freiburg in Germany to produce the new structure using metamaterials (materials that show non-natural properties with the use of carefully engineered structures).
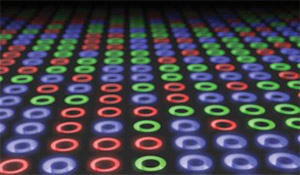
The structure is made of tiny (micro-scale) cavities etched into the surface of silicon. Terahertz waves that hit the structure are captured and compressed inside the cavities.
“By tailoring the silicon properties through the use of micro-structures (the size of a cross-section of human hair) it is possible to trap and confine the waves in a volume much smaller than the wavelength of the terahertz waves,” said Dr. Withayachumnankul. “This significantly improves the efficiency of terahertz devices, such as scanners, and will have broad impact on biomedicine and homeland security, where better contrast means more accurate identification.”
RMIT team leader Dr. Sharath Sriram said, “We needed to carefully select appropriate materials and processes to produce this device. We couldn’t construct the micro-cavities in our first choice of material, so we changed to silicon, which we had to adapt to make it slightly electrically conductive. We then used established silicon microfabrication techniques to create the micro-cavities, exploiting the conductive properties.”
The new structure could be added to conventional terahertz imaging devices to enhance their performance.
The research was supported by the Australian Research Council and partially by a Victoria Fellowship to Dr. Sriram.