Cyber Caliphate Attacks Malaysia Airlines Website
- By Ginger Hill
- Jan 26, 2015
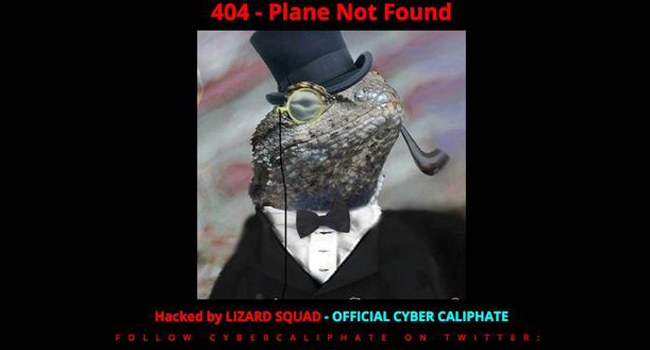
As Malaysia Airlines tries to rebound after Flights 370 and 17 (MH370, MH17), a group calling itself “Cyber Caliphate” had other plans. Hacking into Malaysia Airlines’ website, messages like “ISIS WILL PREVAIL,” “404-Plane Not Found” and “Hacked by Cyber Caliphate” were displayed in strategic areas, such as at the top of the browser’s window, and some were accompanied by graphics, one including a picture of Malaysia Airlines A380.
Later, an image of a tuxedo-wearing, pipe-smoking lizard with a top hat and monocle appeared, with “Hacked by Lizard Squad, Official Cyber Caliphate,” giving the Twitter handle for a group called Lizard Squad. This is the same group who claimed responsibility for the cyberattack on Sony and Microsoft’s videogame servers in December 2014.
In response, Malaysia Airlines replaced the hacked site with a version that allowed users to book flights. The airline immediately reported this incident to CyberSecurity Malaysia, a forensics and analysis agency directed by the Ministry of Science, Technology and Innovation and the Ministry of Transport.
“Our investigation determined that it was a case of domain hijacking,” said CyberSecurity Malaysia Chief Executive Amirudin Abdul.
Malaysia Airlines have since released a statement indicating that their Web servers are intact and customer bookings and data are secure.
Image from the UK's Mirror website.
About the Author
Ginger Hill is Group Social Media Manager.