Firewall Protection
Vital information among the most coveted resources
- By Patrick E. Craig
- Feb 01, 2015
Money Movers Inc. is a fully PCI DSS compliant Electronic
Funds Transfer Gateway processor. In plain English, that
means we move a lot of data over a network. If we could not
protect this information from unfriendly eyes, we would be
out of business quickly and completely. So, the IT department
works diligently to protect client information. That means it is necessary to
have ironclad, hack-proof firewalls in place.
You probably know that you need firewall security; in fact, you may even already
have a firewall management program in place. But, what exactly is firewall
security? How do you apply it to your servers, and how do you stay abreast of not
only the most current developments in protection, but also the most dangerous
new Internet threats?
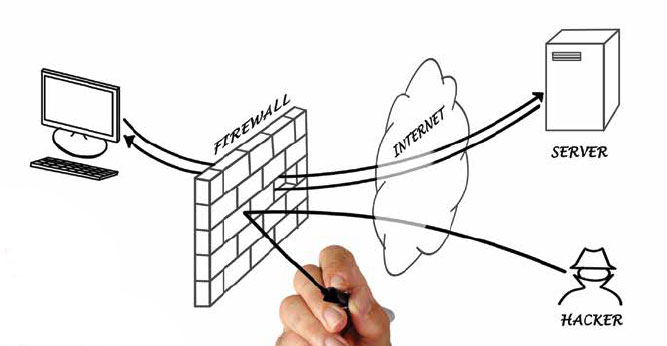
At their most basic, firewalls work like a filter between your computer/network
and the Internet. You can program what you want to go out of your server and
what you want to get in. Everything else is not allowed. Corporations like Money
Movers Inc. often have very complex firewalls in place to protect their extensive
networks. But here’s the problem: firewalls do not focus specifically on preventing
hacking, and hacking has proven to be the biggest threat to any company that
handles sensitive information through its networks.
“Cyber Hacking is a silent stalking time-bomb that threatens all Internet connections
twenty-four hours a day, seven days a week,” said George Baldonado,
president and CEO of Oasis Technology. “Most companies, corporations, and
agencies don’t even know that it’s happening to them.
According to Baldonado: Armies of Cyber Hackers from all over the world are
targeting our infrastructure, military, data, intellectual property, innovations, our
ideas, and even our identity information. At their disposal are thousands of foreign
computer ‘bots’ that churn out thousands of hack attempts per millisecond
looking to gain a millions of dollars’ worth of information. Sooner or later the
targeted network will fold or open up. Once it folds, either the network or application
will crash, or worse, the data will be compromised.
“This affects all companies and agencies that use, store, or access sensitive information.
It doesn’t matter whether the company is a doctor’s office, CPA office,
military, state, county or state agency. Even companies that just process their charge
cards using PC’s are vulnerable. Additionally, each of the millions of cyber hack
attempts also congests the company’s network bandwidth until the bandwidth is so
full of hack attempts that normal business cannot be transacted,” said Baldonado.
All you need to do is follow the stories about the massive hacks perpetrated on
Target, Home Depot, Chase and other multi-national companies to realize that we
are living in an era of rampant Internet thievery where anyone who has sensitive
data of any kind is at risk if they do business electronically.
If you’re terrified, you probably will ask what you can do to bring your network
up to premium levels of protection.
There is a solution. Oasis Technology has come up with a solution that we have
implemented at Money Movers Inc., The Oasis TITAN Network Security Systems.
TITAN is not a Firewall—its sole purpose is to protect and fortify firewalls
to ensure data really is secure. After we put our TITAN into our server system we
were able to document hundreds of hack attempts a week, many from China, and
TITAN was turning them all away.
Oasis built TITAN because they had been mistaken for a processing gateway
company with a slightly different name and by 2012 had become the focus of unrelenting
cyber-attacks. So they developed TITAN to protect themselves. It worked
so well that they began offering the device to other companies whose firewalls had
significant holes and deficiencies in their architecture.
The system is designed for optimum performance regardless of location, network
type, PC or MAC, Microsoft or Linux. Unlike traditional companies, Oasis
also provides a comprehensive security audit to add further protection based upon
industry security methods and procedures.
Oasis engineers can customize TITAN to integrate with a customer’s legacy
security infrastructure.
This article originally appeared in the February 2015 issue of Security Today.
About the Author
Patrick E. Craig is a published author and blogger who writes regularly about the Electronic Funds Transfer and Automated Clearing House industry in his column ACH Review.