Search Warrant Required Before Using Secretive Cellphone Surveillance
- By Ginger Hill
- Sep 14, 2015
Representing the first effort to create uniform legal standards for federal authorities using equipment such as cell-site simulators to track cellphones, a search warrant must now be obtained before using this secretive and intrusive technology. This new policy was announced by the Justice Department on Thursday, September 3, 2015.
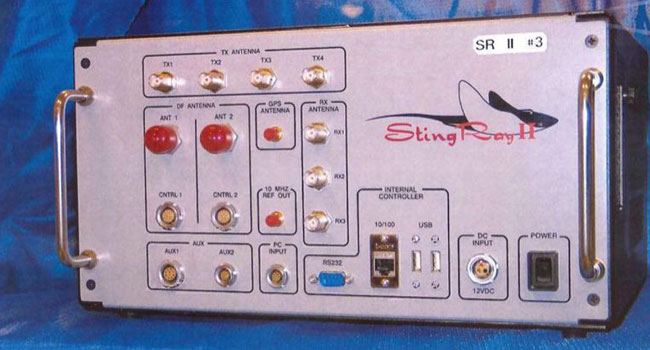
This technology is known as Stingray, a suitcase-sized device that can sweep basic cellphone data from a neighborhood by tricking phones in the area to believe that it’s a cellphone tower. This allows the device to identify unique subscriber numbers. The data is transmitted to police to help them determine the location of a cellphone without the cellphone user making a call or sending a text.
Privacy groups and lawmakers have stated their concerns about local police departments infringing on privacy rights by using this technology. This policy, though, only applies to federal agencies within the Justice Department, not state and local law enforcement, like some groups had hoped for. Still, as federal law enforcement officials praise this technology as a valuable tool to catch fugitives and other criminals, privacy groups fear the secrecy surrounding it and the collection of innocent bystander’s data that just happen to be in a particular location.
The Justice Department seems mindful about these concerns, specifying the policy indicates that in most cases, except for emergencies like national security threats, a warrant must be obtained. Additionally, authorities are required to delete all collected data once they have obtained the data they needed. Training is expected to be provided to all employees.
How do you feel about this new policy? Would you feel as though your privacy was violated if your cellphone data was obtained by Stingray?
About the Author
Ginger Hill is Group Social Media Manager.