John Oliver Cracks the Encryption Argument
- By Sydny Shepard
- Mar 14, 2016
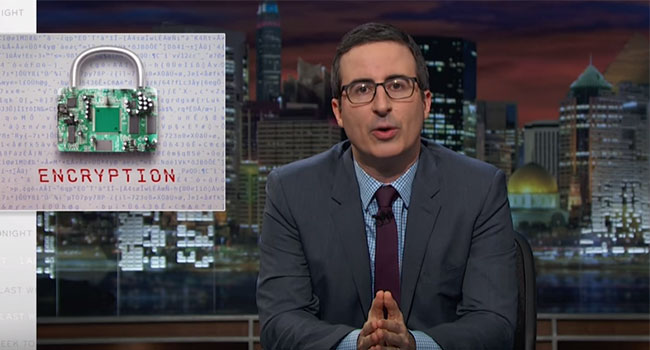
John Oliver, host of the popular HBO talk show Last Week Tonight, attempted to explain the encryption battle between Apple and the FBI for his viewers.
Lately, the industry has been turned upside down by the constant battle between Apple and the FBI. The high-tech issue of encryption has stayed firmly in the headlines for over a month as the FBI fights Apple in court, asking for a way to forgo the security methods on the iPhone in order to break into San Bernardino shooter, Syed Farook’s iPhone. While it sounds like a pretty straight-forward case, Oliver explains that it is actually, “hugely complicated.”
Apple Time Cook has gone on record as saying an Apple “Master Key” to the iPhone would be problematic for all who implement the device in their daily lives. It would make all iPhone users vulnerable to attack by hackers, cybercriminals and others who would like to gain access to the data stored on people’s iPhones. As Oliver notes, if Apple was able to give the FBI what they wanted, it would be likely that China and Russia would demand similar access to the iPhones of their countries.
Apple is also worried that by breaking into Farook’s phone, they would be inundated with encryption-cracking requests from law enforcement all around the world. “Think of the government like your Dad,” Oliver said. “If he asks you to help him with his iPhone, be careful. If you do it once, you’re going to be doing it 14 times a day.”
Basically, Oliver said it’s not quite like “giving a house key to a trusted neighbor,” but a complex issue with wide-reaching ramifications. See what Oliver had to say in more in this clip from Last Week Tonight.
About the Author
Sydny Shepard is the Executive Editor of Campus Security & Life Safety.