Vivint Looks to Expand Smart Home Security to Your Neighborhood
Vivint has introduced a free app called, "Streety" which allows neighbors to share live video feeds from their home security cameras.
- By Sydny Shepard
- Jan 09, 2018
Smart homes and all the cool tech that goes along with them really made an impact on the security industry in 2017, but now, some companies are looking to expand how far home security really goes.
While outdoor security devices and cameras are a great crime deterrent, they are also useful to help identify a person who wasn't chased off your property by automatic flood lights and night vision cameras. The biggest issue with providing forensic evidence to help police apprehend criminals is that you can't really catch everything that is going on with just one or two cameras around your home.
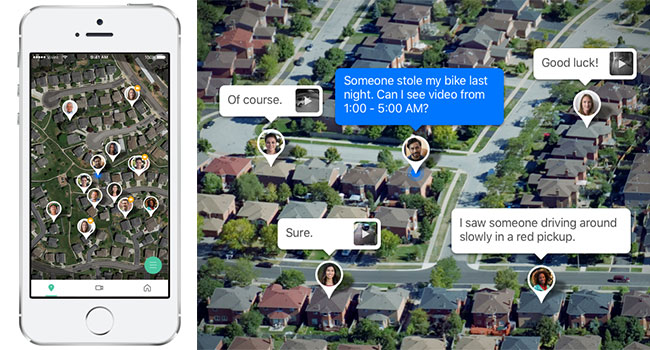
Security company, Vivint Smart Home is looking to give the average smart home security system a boost in functionality by allowing the users in the same neighborhood to share and exchange live video feeds and recorded clips from their home security cameras. The app, called "Streety" is expected to roll out in the spring to everyone in the U.S. and Canada.
Neighbors who choose to participate will be able to form a private network of security cameras inside a 300-yard radius. The boundary is intended to ensure that requests only come from nearby neighbors and not someone trying to take advantage of the app. A third-party verification service will match the identities and addresses of each Streetly user.
Perhaps the best part of Vivints new app is that you don't need to be a Vivint subscriber or have a Vivint camera - or any camera at all - to become apart of the smart neighborhood watch. The objective is to build stronger communities, said VP and general manager Clint Gordon-Carroll.
The app could change the way people feel safe in their homes and could revolutionize the idea of a Neighborhood Watch. Using Streetly, neighbors can post messages and videos to help each other investigate break-ins, vandalism, stolen packages and other incidents. Users will also be allowed to stream live video, from Vivint cameras at least, to monitor their children playing in a friend's yard or to keep an eye on a neighbor's home while they are on vacation.
Vivint says it has developed Streety as an open platform and is inviting other camera manufactures to integrate the app into their own products.
About the Author
Sydny Shepard is the Executive Editor of Campus Security & Life Safety.