China Reportedly Used Microchips to Infiltrate U.S. Companies
The claims have been strongly disputed by the technology companies.
- By Sydny Shepard
- Oct 05, 2018
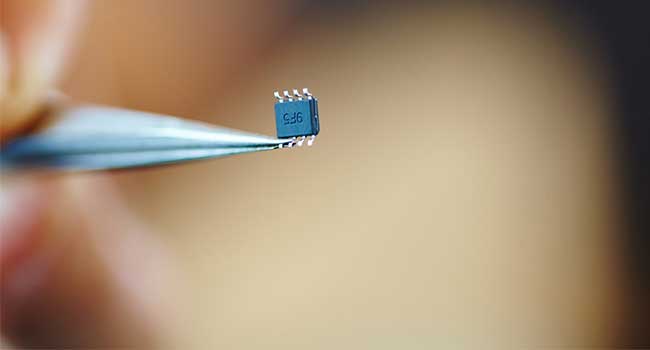
Data center equipment run by tech giants, such as Amazon Web Services and Apple, may have bee infiltrated by the Chinese government by a tiny microchip inserted during the equipment manufacturing process, according to a stunning Bloomberg BusinessWeek report. The companies named in the report have strongly denied the claims.
BusinessWeek explains that the chips had been the subject of a secret U.S. government investigation since 2015 and were used for gathering intellectual property and trade secrets from American companies. The chips may have been introduced by a Chinese server company called Super Micro that assembles machines used in the centers.
BusinessWeek reports that the problem was discovered in 2015 and confirmed by independent security investigators hired by the cloud providers. Super Micro servers were removed by Apple that year, according to the report, which also says that ties between Apple and Super Micro were severed the following year. A follow-up investigation involving several government agencies followed.
Apple, AWS and Super Micro have all vehemently disputed the report by BusinessWeek, which heavy relies on anonymous government and corporate sources. Apple said it did not find the chips and Super Micro denied having introduced the chips during manufacturing.
"We are deeply disappointed that in their dealings with us, Bloomberg's reporters have not been open about the possibility that they or their sources might be wrong or misinformed. Our best guess is that they are confusing their story with a previously reported incident in 2016 which we discovered an infected driver on a single Super Micro server in one of our labs," Apple said in a statement to CNBC. "That one-time event was determined to be accidental and not a targeted attack against Apple."
Intellectual property theft is one of the core arguments for touch trade restrictions on China by the Trump administration. China has been long suspected in spy campaigns based on hardware made there.
In a statement to Security Today, Head of Hardware Security at F-Secure Andrea Barisani says he's skeptical of the report.
"It is certainly possible to mount supply chain attacks that can affect the security of COTS (Commercial Off The Shelf) hardware, albeit posing notable implementation difficulties," Barisani said. "If anything, there are only official denials on the story and the lack of technical details doesn't really favor the conclusions from a technical standpoint."
Moving forward, CEO of Fortanix Ambui Kumar says U.S. companies need to carefully vet their supply chain.
"Unfortunately, foreign countries manufacture most of our chips and systems, so it’s going to be tricky to protect against motivated nation-state actors," Kumar said in a statement to Security Today. "However, there is at least one component that is designed and integrity-controlled in USA, the CPU. Most of the new CPUs offer secure enclaves that keep applications and data protected even when such hardware implants are present. Enclaves are new but proven ways to protect sensitive data. If we cannot keep hardware implants away, may the best thing is to ensure security even when they are present."
About the Author
Sydny Shepard is the Executive Editor of Campus Security & Life Safety.